On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
User provisioning is the process of creating, managing, and removing user accounts and access rights across enterprise systems based on identity, role, and policy. It ensures users receive the right access at the right time while maintaining security, compliance, and least-privilege access.
User provisioning plays a critical role in identity and access management (IAM) by ensuring that access to systems, applications, and data is granted, modified, and revoked accurately throughout a user’s lifecycle.
Access management failures remain a significant operational and security challenge. According to Gartner, 50% of help desk requests are related to permissions, and human error accounts for more than 80% of access misconfigurations. As organizations scale across cloud and SaaS environments, these risks compound rapidly when provisioning relies on manual processes.
Automated user provisioning addresses this challenge by enforcing consistent access policies, improving auditability, and reducing reliance on human intervention. In 2025, it is no longer an optimization, it is a baseline requirement for scalable, identity-driven security. Understanding how provisioning works, and why it matters, is essential for maintaining control across modern enterprise environments.
Key Takeaways
- User provisioning is a foundational component of secure identity and access management (IAM).
- Automation reduces operational overhead, limits access risk, and supports regulatory compliance.
- Common provisioning models include manual, automated, SCIM-based, role based, and self-service provisioning.
- A complete lifecycle spans onboarding, access updates, role changes, and deprovisioning.
- Best practices include enforcing least privilege, automating access decisions, conducting regular access reviews, and integrating multi-factor authentication.
What Is User Provisioning?
User provisioning controls how user access is granted, updated, and revoked across systems using IAM policies, automation, and role-based controls to reduce security risk and operational overhead.
User provisioning defines how user access is granted, updated, and revoked across systems using identity and access management (IAM) policies, automation, and role-based controls. Its purpose is to ensure access is consistently aligned with organizational requirements while reducing security risk and operational overhead. In practice, user provisioning manages the full identity lifecycle—from onboarding and role-based access assignment to access updates and deprovisioning as responsibilities change or end. By automating these processes, organizations limit manual effort, reduce configuration errors, and maintain timely, auditable access to systems, applications, and data in line with security and compliance standards.
Core Elements of User Provisioning
Identity creation and lifecycle management
Establishes and maintains user identities from onboarding through offboarding.
Role- and policy-based access assignment
Aligns permissions with job functions using predefined roles and access policies.
Automated access updates
Adjusts access dynamically as users change roles, teams, or employment status.
Deprovisioning and access revocation
Ensures access is promptly removed when no longer required to prevent residual risk.
Auditability and compliance support
Provides visibility and traceability for access decisions to meet regulatory and internal requirements.
Pro Tip
User provisioning fails most often when roles are defined too broadly. Start with minimum viable roles, then expand access only when usage data proves it’s needed. This prevents over-provisioning from day one.
Definition of User Provisioning
User provisioning refers to automating the creation, updating, and deletion of user accounts and access permissions in an organization’s systems, typically as part of identity and access management(IAM).
By automating provisioning workflows, organizations replace manual, error-prone processes with standardized controls that operate across the user lifecycle. New users receive required access promptly, access is adjusted as roles change, and permissions are reliably revoked when users exit the organization. This approach eliminates dependency on ad hoc tracking methods and improves consistency at scale.
Outcomes of Effective User Provisioning
Faster and more consistent onboarding
Users receive appropriate access from day one without administrative delays.
Reduced orphaned and residual access
Access is reliably revoked during offboarding to prevent dormant or unmanaged accounts.
Elimination of manual access tracking
Centralized workflows replace spreadsheets and fragmented processes.
Overall, user provisioning consolidates security, operational efficiency, and compliance into a single, enforceable process that scales with organizational growth.
Why Is User Provisioning Important?
User provisioning is critical because it directly impacts security posture, operational efficiency, audit readiness, and breach prevention. Poor provisioning is one of the leading causes of unauthorized access and compliance failures.
User provisioning extends far beyond simply setting up accounts; it’s crucial to running a secure and efficient business. When done right, it protects your data, keeps teams productive, and helps you stay compliant. In a digital world where access needs are constantly evolving, getting it right matters more than ever. Let’s take a look at why it’s so important:
Not Sure How Strong Your Provisioning Is?
Check it with the User Provisioning Readiness & Risk Scorecard
1. Security
Effective user provisioning ensures that access is granted strictly according to role, policy, and business need. This reduces exposure to insider risk, limits excessive permissions, and prevents dormant or over-privileged accounts from becoming attack vectors. In distributed and remote environments, automated provisioning enables consistent enforcement of access controls across applications, devices, and cloud platforms.
2. Operational Efficiency
Automated provisioning streamlines onboarding, role changes, and offboarding by removing manual intervention from access workflows. New users receive required access without delay, while access is promptly revoked when users leave or change roles. This reduces IT workload, eliminates bottlenecks, and ensures access transitions occur predictably across departments.
3. Compliance
Regulatory compliance refers to an organization’s ability to meet legal and industry-specific standards such as GDPR, HIPAA, SOX, and PCI DSS, each of which mandates strict control over user access to sensitive data. User provisioning plays a critical role in helping organizations meet these requirements by enforcing the principle of least privilege, maintaining comprehensive access logs, and ensuring that user access is granted, modified, or revoked on time. When integrated with identity lifecycle management (ILM), provisioning automates access enforcement, preserves audit trails, and simplifies access reviews. Embedding these controls into daily operations improves audit readiness and reduces the likelihood of violations or penalties.
4. Risk Reduction
Automated user provisioning helps prevent privilege creep and the presence of orphaned accounts by promptly revoking access rights when users exit the organization or transition to new roles. By utilizing role-based access control (RBAC) and implementing policy-driven provisioning, organizations can consistently apply the principle of least privilege, ensuring that users are granted access only to the resources necessary for their responsibilities. Furthermore, conducting regular access reviews and certification campaigns enables organizations to validate and update user entitlements, thereby reducing the overall attack surface and enhancing the organization's security posture.
Reality Check:
If your access reviews happen only before audits, your provisioning process is already broken. Governance should run continuously, not just when compliance deadlines loom.
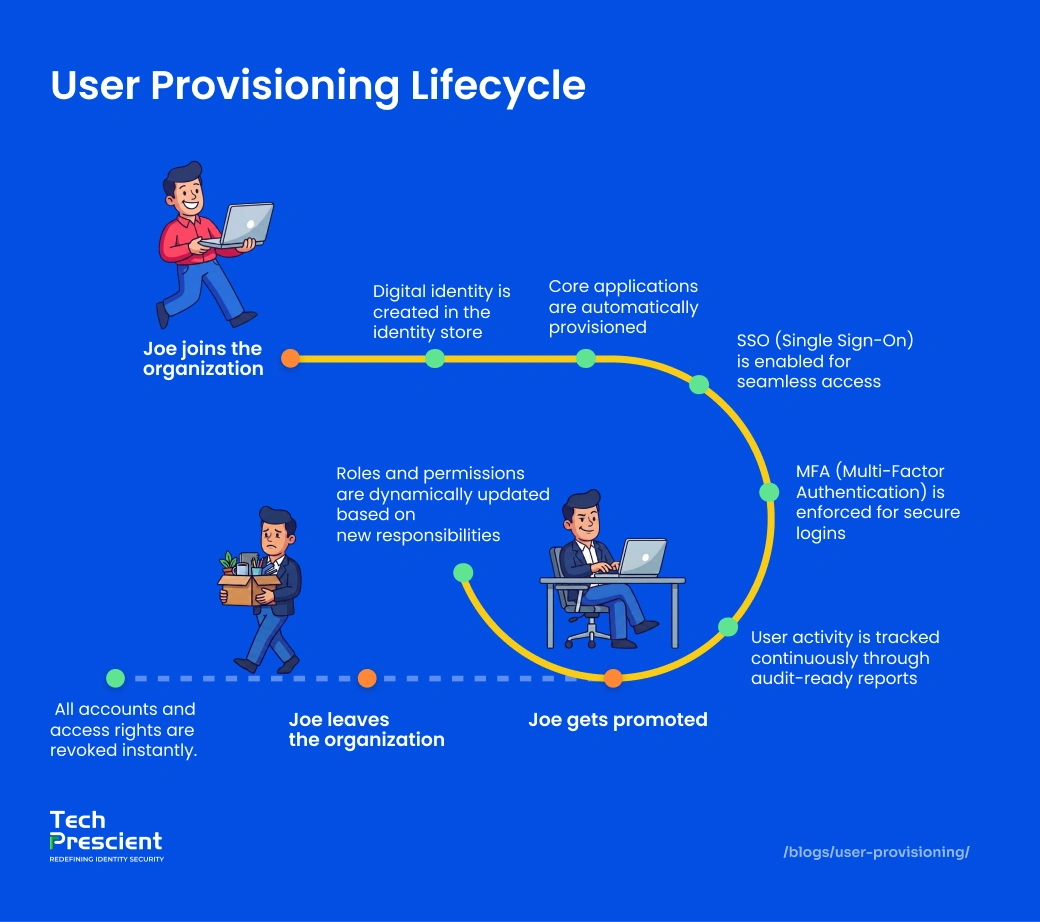
User Provisioning Lifecycle (Joiner–Mover–Leaver Model)
Most enterprises follow a Joiner–Mover–Leaver (JML) model to govern user access throughout the identity lifecycle. This model ensures access is granted when users join, adjusted when roles change, and revoked immediately when users exit.
Account Creation
The user provisioning process starts when an HR or onboarding system sends a signal to create a new account. This automatically sets up the user in all the necessary systems, eliminating the need for manual work. It ensures every new user is set up properly and consistently. The result? Faster onboarding with fewer errors or duplicate accounts.
Role Assignment & Access Granting
Once an account is created, access is assigned based on role, department, or defined attributes. Role-based access control (RBAC) or attribute-based access control (ABAC) models are commonly used to automate permission assignment in accordance with policy. This stage enforces the principle of least privilege by granting only the access required for the user’s responsibilities.
Modification During Role Changes
As people change roles, switch teams, or take on new projects, their access needs to change too. This part of the user provisioning process keeps permissions up to date in real time. Without it, someone might lose access they need, or keep access they shouldn’t have. Both can cause security risks and slow down productivity.
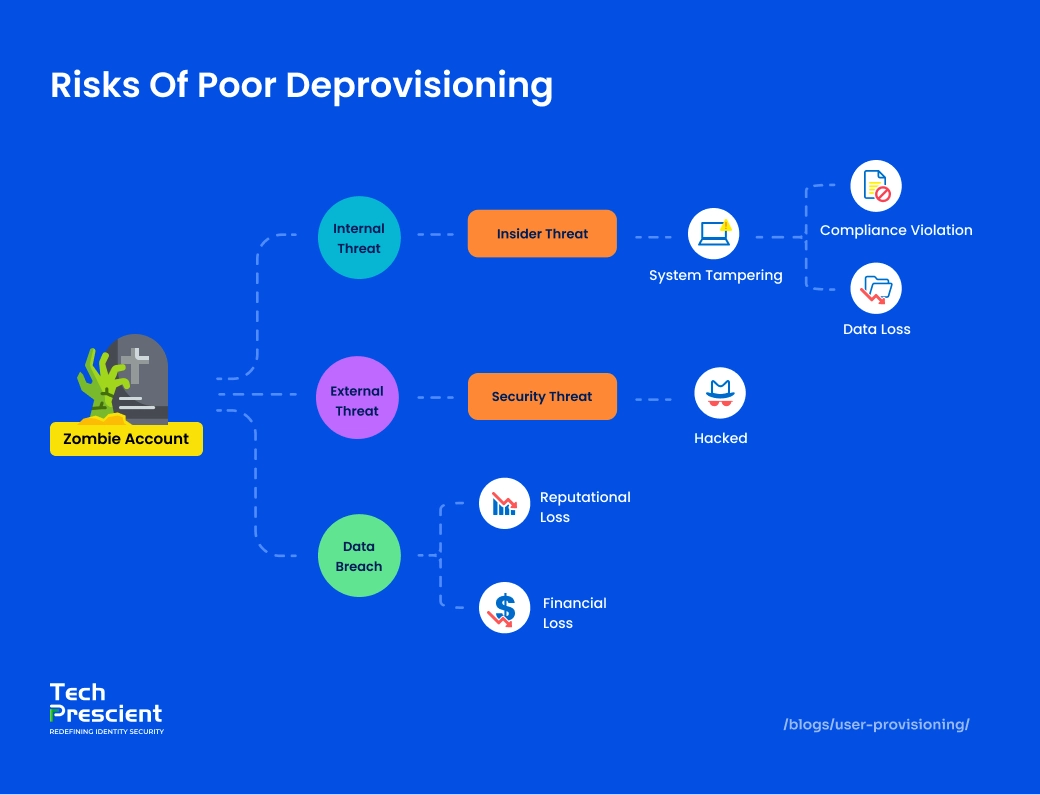
Deprovisioning
When a user exits the organization or no longer requires access, the final stage in the user provisioning lifecycle is deprovisioning. This process leverages automation to revoke permissions, terminate active sessions, and disable user accounts across all integrated systems. By preventing orphaned accounts and unauthorized access, deprovisioning strengthens security posture and supports regulatory compliance, particularly critical in enterprise environments.
What Are the Types of User Provisioning?
User provisioning methods range from manual and role-based approaches to fully automated, self-service, and SCIM-based models, each offering different levels of scalability, control, and security.
The user provisioning lifecycle can take many forms depending on your organization’s size, tools, and security needs. From manual setups to fully automated and role-based models, each approach offers different levels of efficiency and control. Understanding the types of user provisioning helps you choose the right method for scaling securely and effectively.
1. Manual Provisioning
Manual provisioning requires administrators to create user accounts and assign access individually within each system. While feasible for very small environments, this approach does not scale and introduces significant risk as user volume grows. Manual workflows are prone to delays, configuration errors, inconsistent access enforcement, and limited auditability, making them unsuitable for environments with compliance or security requirements.
2. Automated Provisioning
Automated provisioning uses predefined workflows to assign access based on identity attributes or roles. When a user is assigned a role, accounts and permissions are provisioned automatically across connected systems. This approach eliminates repetitive administrative tasks, reduces human error, and ensures access is applied consistently across applications and cloud services.
Not Sure How Strong Your Provisioning Is?
Check it with the User Provisioning Readiness & Risk Scorecard
3. Role-Based Access Control (RBAC)
Role-based access control (RBAC) provisions access according to predefined job roles, such as finance, engineering, or human resources. Each role maps to a standardized set of permissions, allowing access to be managed at scale without assigning entitlements individually. RBAC improves consistency, simplifies administration, and supports least-privilege enforcement when roles are properly defined and governed.
4. Self-Service Provisioning
Self-service provisioning lets users request access to tools or apps through a simple portal. Requests go through automated approval steps, so users get what they need faster, without IT losing control. It cuts down wait times and avoids the back-and-forth of manual tickets. Everyone wins with faster, smoother access.
5. SCIM Provisioning
SCIM (System for Cross-domain Identity Management) is an open standard that automates the exchange of user identity data between identity providers and cloud apps. It handles provisioning, updates, and deprovisioning in real time using standardized REST APIs. This reduces manual effort, keeps identities in sync across systems, and is ideal for managing access in multi-cloud environments.
How Does User Provisioning Work?
User provisioning workflows are triggered by authoritative sources such as HR systems, synced across identity platforms, mapped to roles or policies, and automatically enforced across applications with continuous audit tracking.
User provisioning involves several coordinated steps to ensure users have the right access at the right time. From onboarding to deprovisioning, each stage plays a critical role in maintaining security, efficiency, and compliance. Here’s how the user provisioning workflow typically unfolds behind the scenes.
Trigger
The process begins when a new hire is added to the HR system, like Workday or BambooHR. That update sends a signal to identity systems to start setting up accounts. Since it all starts with HR, the source of truth, everything stays accurate and in sync. It’s a simple, automated way to launch the user lifecycle.
Identity Sync
The IAM system keeps user info synced across all platforms, apps, directories, and services. That means no more entering the same details in multiple places. If something changes, like a job title or department, it updates everywhere automatically. It’s a smooth way to keep identity data accurate and up to date.
Role Mapping
Access is given based on a person’s job role or other details, using models like RBAC or ABAC. This makes sure users only get access to what they need for their work. It helps avoid giving too much access by mistake. The result? Better security and fewer manual errors.
Access Provisioning
Once access is mapped, the right permissions are automatically given for the tools a user needs, like email, collaboration apps, or finance systems. Everything is tracked for auditing, so there’s a clear record. The best part? The user gets instant access without waiting on IT. It’s fast, secure, and hassle-free.
Deprovisioning
Deprovisioning refers to the process of modifying or removing user access when an individual leaves the organization or transitions to a different role. This ensures that access permissions are updated to reflect the user’s current status, helping prevent the existence of unused or orphaned accounts. Proper deprovisioning is critical for maintaining system security, minimizing the risk of unauthorized access, and ensuring that identity and access data remains accurate and up to date. Even routine updates like these play a significant role in reducing security vulnerabilities and strengthening overall access governance.
Provisioning vs. Deprovisioning
Provisioning and deprovisioning together form the foundation of secure identity lifecycle management by ensuring access is both granted and removed at the right time.
Provisioning
Provisioning is the process of granting users access to systems, applications, and data based on their role, department, or other identity attributes. It ensures that employees are equipped with the necessary resources from day one, enabling immediate productivity and reducing onboarding delays. Provisioning typically includes account creation, role-based permission assignment, and application access setup, automated through IAM systems to minimize manual intervention and reduce the risk of errors. An effective provisioning process not only accelerates user onboarding but also enforces consistent access policies and centralizes control.
Deprovisioning
Deprovisioning refers to the timely removal or adjustment of access rights when a user leaves the organization or no longer requires specific resources. It is a critical component of access lifecycle management, playing a key role in maintaining security and regulatory compliance. By revoking access promptly, organizations can prevent potential data breaches, eliminate orphaned accounts, and reduce their overall attack surface. Automated deprovisioning ensures that user access is terminated across all connected systems, helping to close security gaps and complete the user lifecycle in a controlled and compliant manner. Together, provisioning and deprovisioning form the foundation of secure and policy-driven identity management.
What Are the Benefits of User Provisioning?
Implementing user provisioning brings measurable benefits across security, efficiency, and compliance. By automating access management and aligning it with business roles, organizations can reduce risk, streamline operations, and maintain better control over user activity. Let’s explore the key advantages it offers.
1. Improved Security
User provisioning enforces the principle of least privilege by ensuring users receive only the access required for their roles. Automated access controls reduce excessive permissions, limit insider risk, and prevent dormant or outdated access from becoming an attack vector.
2. Faster Onboarding/Offboarding
Provisioning automation enables timely access during onboarding and immediate access revocation during offboarding. This eliminates delays in productivity while ensuring that access is not retained beyond its intended lifecycle, reducing both operational friction and security exposure.
3. Reduced IT Workload
By automating repetitive access management tasks, user provisioning reduces manual administrative effort. This allows IT and security teams to focus on higher-value initiatives such as governance, risk reduction, and system optimization rather than routine account maintenance.
4. Enhanced Compliance
Automated provisioning systems generate comprehensive audit logs for all access-related activities, such as account creation, role assignments, and deprovisioning, ensuring complete traceability for compliance audits under standards like GDPR, HIPAA, and SOX. By applying policy-driven access controls and aligning provisioning workflows with regulatory requirements, these systems ensure that access is consistently granted and removed as needed. This not only minimizes the risk of human error or policy violations but also simplifies audit preparation and reduces the operational burden on IT teams.
5. Centralized Access Control
Centralized provisioning provides a unified view of user access across applications and systems. This visibility supports ongoing access reviews, detection of anomalous permissions, and consistent enforcement of security policies across the environment.
6. Streamlined User Management Across Systems
User provisioning simplifies management by automatically syncing user data from sources like Active Directory (AD), LDAP, and other integrated applications. It ensures user profiles stay current across all connected systems, reducing manual updates and keeping information accurate at all times. This improves consistency and minimizes the risk of outdated or incomplete user data.
Challenges in Scaling Provisioning
Scaling user provisioning becomes increasingly complex as organizations expand, adopt additional cloud and SaaS platforms, and integrate external systems. Inconsistent policy enforcement, legacy processes, and fragmented identity data introduce friction that can undermine security, compliance, and operational efficiency.
1. Inconsistent policies across tools
As organizations adopt more applications and cloud services, access policies are often defined and enforced independently within each system. This fragmentation leads to duplicated roles, inconsistent permissions, and gaps in access control. Without centralized policy governance, organizations struggle to maintain consistent security standards across the environment.
2. Growing pains during mergers or hypergrowth
Mergers, acquisitions, and periods of rapid growth significantly increase the volume and diversity of identities, systems, and access requirements. Without automated provisioning and clearly defined policies, onboarding new users and integrating systems can introduce delays, inconsistencies, and elevated risk.
3. Manual errors in legacy systems
Legacy identity systems frequently rely on manual provisioning processes or custom scripts. These approaches increase the likelihood of configuration errors, limit auditability, and make access changes difficult to track. As scale increases, manual dependency compounds risk and operational overhead.
4. Keeping identity data clean and current
Effective provisioning depends on accurate identity data from authoritative sources. Incomplete, outdated, or duplicated records can result in incorrect access assignments or failed workflows. Maintaining synchronization across HR systems, directories, and IAM platforms is critical for reliable and secure provisioning at scale.
Scaling Insight
Provisioning complexity doesn’t grow linearly, it explodes with every new SaaS app. Without centralized governance, each new tool multiplies access risk instead of productivity.
Not Sure How Strong Your Provisioning Is?
Check it with the User Provisioning Readiness & Risk Scorecard
Best Practices for User Provisioning
To ensure secure, efficient, and scalable user provisioning, it's essential to follow structured best practices. From automating access management to enforcing the principle of least privilege and regular audits, these strategies help reduce risk, improve compliance, and streamline operations across the user lifecycle.
1. Automate Whenever Possible
Leverage identity and access management tools with built-in automation to efficiently handle user onboarding, access modifications, and timely deprovisioning. Automated workflows reduce manual errors, improve consistency, and ease the administrative burden on IT teams. These solutions are designed to scale seamlessly with complex IT environments, accommodating the addition of new systems, applications, and user roles without compromising control or performance. It’s a reliable, efficient, and scalable approach to identity and access management.
2. Apply Principle of Least Privilege
Provision access strictly according to role, policy, or defined attributes, and remove permissions when they are no longer required. Limiting access to the minimum necessary reduces exposure, prevents permission sprawl, and strengthens overall access governance.
3. Standardize Onboarding/Offboarding
Implement standardized provisioning and deprovisioning workflows using predefined templates and approval paths. Consistent execution reduces the likelihood of missed access changes, improves auditability, and ensures predictable access outcomes across departments and systems.
4. Conduct Regular Access Reviews
Perform periodic access reviews to identify and remediate excessive or outdated permissions. Automated certification processes and clearly defined review policies help prevent privilege accumulation over time and ensure continued alignment between access entitlements and business responsibilities.
5. Use MFA & Risk-Based Authentication
To enhance identity and access security, Identity and Access Management (IAM) systems utilize Multi-Factor Authentication (MFA) along with risk-based adaptive authentication. MFA requires users to authenticate their identity using multiple independent factors, commonly including something they know (like a password), something they have (such as a hardware token or mobile authenticator), and something they are (biometric identifiers).
Risk-based authentication strengthens security by dynamically analyzing contextual risk factors, such as device type, geolocation, IP address reputation, time of access, and user behavior, during each login attempt. Based on the level of assessed risk, the IAM system can apply adaptive access controls in real time, which may include prompting for additional authentication steps, restricting access privileges, or completely blocking access when suspicious or high-risk activity is detected.
This method helps maintain a strong security posture by lowering the chances of unauthorized access while also ensuring a seamless experience for legitimate users through intelligent, context-aware access management.
Real-World Examples & Use Cases
Axos Financial
Axos Financial centralized identity and access management across cloud and on-premises environments to gain control over more than 200,000 permissions. By consolidating provisioning workflows, the organization improved consistency in access enforcement and reduced permission sprawl across departments. Centralization also enhanced audit readiness by providing clearer visibility into access entitlements and simplifying compliance reporting.
CO2 AI
CO2 AI implemented role-based access control (RBAC) to automate user provisioning for globally distributed sustainability teams. Predefined roles aligned with functional responsibilities enabled rapid, policy-driven access assignment while maintaining strict controls over sensitive environmental data. This approach supported secure collaboration at scale without introducing delays or excessive permissions.
User Provisioning in IAM vs. IGA
Identity and access programs commonly distinguish between execution and governance responsibilities. User provisioning spans both identity and access management (IAM) and identity governance and administration (IGA), but each serves a different function within the access control stack.
IAM (Identity and Access Management)
IAM platforms are responsible for executing user provisioning and enforcing access decisions in real time. They automate account creation, role- or attribute-based access assignment, authentication integration (such as single sign-on and multi-factor authentication), and ongoing access enforcement across systems and applications. IAM focuses on the operational question of how access is provisioned, authenticated, and enforced within the environment.
IGA (Identity Governance and Administration)
IGA systems govern provisioning decisions by defining access policies, enforcing segregation of duties (SoD), managing access certifications, and producing audit evidence for compliance. IGA ensures that access assignments align with business intent, regulatory requirements, and internal controls over time. IGA addresses whether a user should have specific access, under what conditions, and with what level of justification.
Key Distinctions
- IAM executes access provisioning and enforcement.
- IGA governs, validates, and audits access decisions.
Together, IAM and IGA form complementary layers of a comprehensive identity security architecture: IAM delivers access, while IGA ensures that access remains appropriate, compliant, and defensible.
Choosing the Right User Provisioning Tool
Choosing the right user provisioning solution is a strategic decision that impacts security posture, scalability, and compliance. The ideal solution should integrate seamlessly with your IAM and IGA ecosystem, support cloud and hybrid environments, and automate identity lifecycle workflows end to end.
Ready to simplify provisioning and strengthen your identity perimeter?
Book a demo with Tech Prescient today.
Not Sure How Strong Your Provisioning Is?
Check it with the User Provisioning Readiness & Risk Scorecard
FAQs
User provisioning in identity management is the automated process of granting, modifying, and revoking user access based on role, policy, and lifecycle events to ensure secure and compliant access control.
Automated user provisioning works by triggering access workflows from authoritative sources like HR systems, assigning role-based permissions, and enforcing access across applications without manual intervention.
RBAC simplifies provisioning by assigning access based on predefined roles, reducing manual errors, enforcing least privilege, and making access reviews and audits easier.
IAM executes provisioning by managing access, while IGA governs provisioning decisions through policy enforcement, access certifications, and compliance oversight.
Yatin Laygude
Content Writer
A content writer with 6 years of experience turning complex topics into clear, engaging, and meaningful content. From blogs and web pages to whitepapers and thought pieces, he creates content that not only explains but also connects with both the audience and business goals.
Most Popular Blogs

Identity Security· 24 min read
RBAC Best Practices for Enterprises: How to Implement Secure Role Models at Scale
Discover top RBAC best practices to secure systems, reduce over-permissioning, and enforce least privilege in identity security.
Yatin Laygude· May 14, 2026