What is Principle of Least Privilege (PoLP)?
Learn what the Principle of Least Privilege (PoLP) is, why it matters in cybersecurity, and how to implement least privilege access effectively.
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Last Updated date: April 10, 2026
Introduction
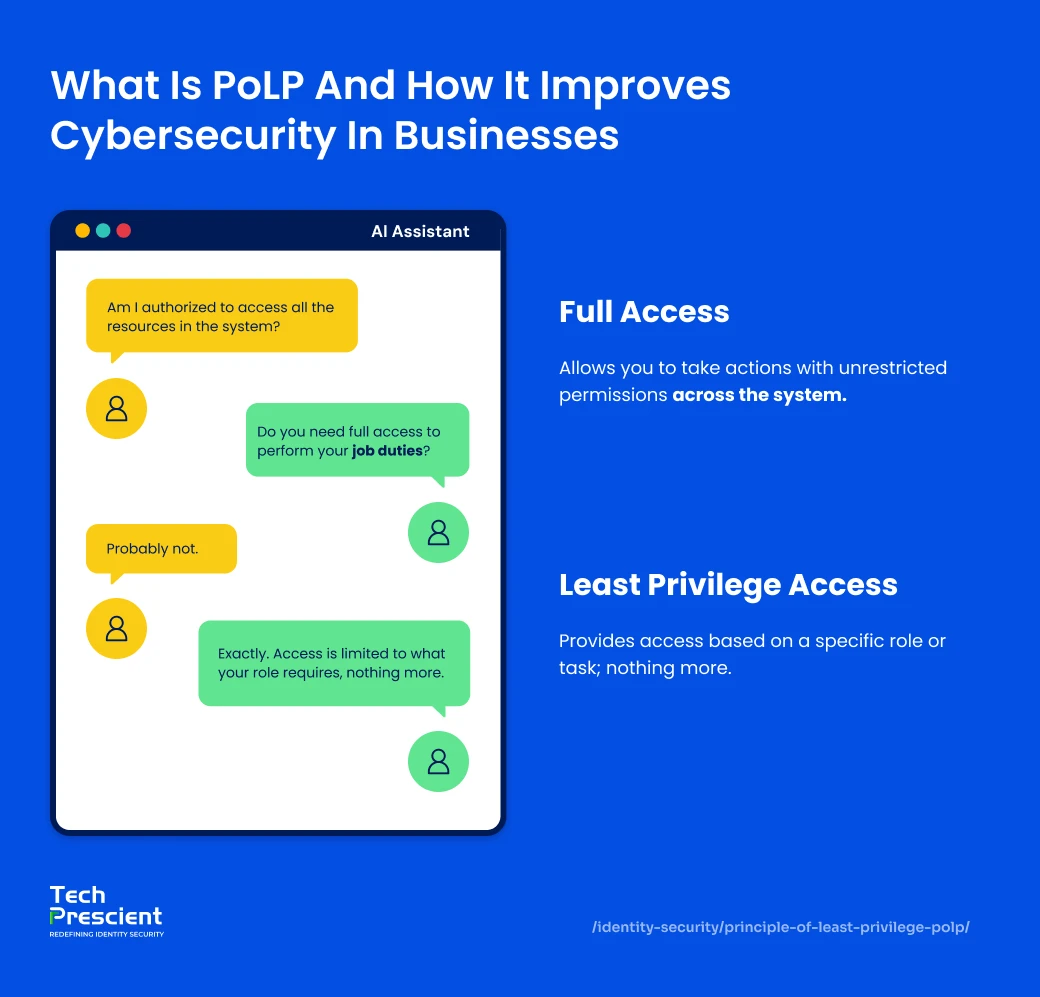
The Principle of Least Privilege (PoLP) is a core cybersecurity practice that restricts users, systems, and applications to only the minimum access required to perform their job; nothing more. By limiting unnecessary permissions, PoLP reduces attack surfaces, prevents privilege abuse, and lowers the risk of breaches caused by compromised or over-privileged accounts.
Whether managing cloud infrastructure, hybrid IT environments, or regulatory compliance requirements, implementing the Principle of Least Privilege helps reduce exposure and operational risk. This article explains what PoLP is, why it matters, and how organizations can apply it using practical, repeatable controls.

What Is the Principle of Least Privilege?
The Principle of Least Privilege (PoLP) is a cybersecurity access control concept that ensures users, applications, and systems are granted only the permissions necessary to complete a specific task and no additional access beyond that. This access control technique minimizes the risk of unintentional mistakes, insider threats, or system compromise by forcing each entity to run under a narrowly defined set of privileges.
According to standard cyber hygiene practices, the Principle of Least Privilege means that users should only have access to the information and systems necessary to perform their job functions. The concept can be illustrated with a simple access control example. Consider access as a set of keys within a secured building. A receptionist requires access to the front desk but not to server rooms or financial systems. When broad access is granted unnecessarily, a single error or compromised account can expose the entire environment. Restricting access by role and responsibility directly reduces this risk.
Why Is Least Privilege Important?
The Principle of Least Privilege (PoLP) is important because it minimizes security risks by reducing unauthorized access, limiting malware spread, and preventing privilege misuse. By limiting access to only what is necessary for a specific role or activity, organizations can significantly reduce the attack surface. This reduces the chances of internal abuse and external attacks.
Adopting PoLP prevents privilege abuse, limits malware propagation, and yields better system stability. It also satisfies audit and compliance needs through traceable and authorized access across the board. PoLP supports a proactive security model by enforcing need-to-know access across users, systems, and applications. This approach reduces the likelihood of accidental exposure while improving visibility and accountability.
Least privilege secures your company's systems and information in significant ways when implemented. It minimizes the threat of unauthorized access, prevents malware from spreading, and prevents internal errors that can cause massive outages or data loss. It's a cornerstone of any contemporary cybersecurity plan.
Industry research consistently shows that compromised or misused privileged credentials are a common factor in security incidents. Limiting privileged access reduces the blast radius when credentials are exposed or misused. Implementing PoLP directly deals with this by limiting the number of users with higher access rights.
When used properly, PoLP not only offers protection but also maximizes overall operational efficiency and audit readiness. Here's a peek at how organizations gain from it on a day-to-day basis
Security Note:
Many breaches don’t start with malware; they start with excessive access. Least privilege reduces the blast radius when credentials are compromised.
Key Principles Underlying the Principle of Least Privilege (PoLP)
Knowing the basis of PoLP makes it easier to understand why it's critical to security. Below is a breakdown of its fundamental purpose and meaning:
What does "Least Privilege" mean?
Least privilege means giving users or systems only the access required to complete their assigned tasks, without granting unnecessary permissions that could increase security risk. Least privilege also becomes apparent in the permissions assigned to view, edit, or execute data and system functions based solely on the user's job role. By limiting access to a strictly role-appropriate basis, organizations can minimize the risks of data exposure, misuse, and breaches directed at internal and external contexts.
Get the Least Privilege Checklist
Use our quick checklist to secure users, apps, and cloud access.

Why is it used?
PoLP allows for better cybersecurity by reducing the potential for malicious or accidental misuse. It avoids data leakage, unauthorized access, and insider threats by granting only the required permissions. It also facilitates audits and compliance by making it easy to monitor who accessed what and when. Lastly, PoLP establishes a better-controlled, manageable, and secure access environment.
Real-World Examples of Least Privilege
Real-world least privilege examples show how limiting access by role prevents outages, data leaks, and compliance violations.
| Scenario | Minimum Required Access | Risk If Over-Privileged |
|---|---|---|
| Software Developer | Access to specific code repositories | Access to production servers could lead to accidental outages |
| External Auditor | Read-only access to audit logs | Write access could compromise data integrity |
| Customer Support Rep | Access to customer profiles | Access to billing systems could expose sensitive data |
These are genuine risks. In big companies, overly privileged users have indeed caused system downtime, data loss, and compliance issues, all due to a lack of granular access control.
A well-known breach at a large financial services firm was due to an over-privileged developer account being exploited by an attacker to access customer financial records. This incident can highlight the essential need for privilege boundaries and ongoing access reviews.
The underlying principle is operational rather than personal: security improves when access controls are defined by role requirements and enforced consistently, rather than relying on individual discretion.
Before we go into how PoLP is the same or dissimilar to Zero Trust, let's establish where they intersect.
Both approaches attempt to achieve minimal risk through access control, but they accomplish it in different ways.
How Is Least Privilege Different from Zero Trust?
Least privilege limits access permissions, while Zero Trust continuously verifies every access request; both work together to reduce security risk. The following distinctions clarify how least privilege and Zero Trust address access risk from different perspectives:
Objective
Risk reduction through permission minimization defines least privilege, while Zero Trust prioritizes continuous verification of every access request, regardless of network location.
Scope
Access boundaries in least privilege are applied to users, applications, and systems. In contrast, Zero Trust evaluates a broader surface that includes devices, network traffic, and identity context.
Enforcement
Authorization frameworks such as RBAC and ABAC are typically used to restrict permissions under least privilege. Zero Trust enforces access through ongoing authentication and session-level controls, including multi-factor authentication (MFA).
Security Assumption
Limiting access is the primary risk-control mechanism behind least privilege. Zero Trust is built on the expectation that compromise can occur and, therefore, requires continuous validation and monitoring.
Operational Integration
As an access control discipline, least privilege often serves as a foundational control, while Zero Trust incorporates it within a broader framework that evaluates access both before and after authorization.
Together, PoLP and Zero Trust create a layered defense approach, where access is both minimized and continuously verified.
| Feature | Least Privilege | Zero Trust |
|---|---|---|
| Goal | Minimize access | Continuously verify access |
| Applies to | Users, apps, systems | Users, devices, network traffic |
| Work together? | Yes, PoLP is part of Zero Trust | Yes, they often support each other |
Get the Least Privilege Checklist
Use our quick checklist to secure users, apps, and cloud access.

How to Use the Principle of Least Privilege in Your Company
We've covered what the Principle of Least Privilege (PoLP) is, how it functions, and its core concepts, and now we're ready to get into how you can implement it. The following steps outline how organizations can implement PoLP in a structured and scalable way.
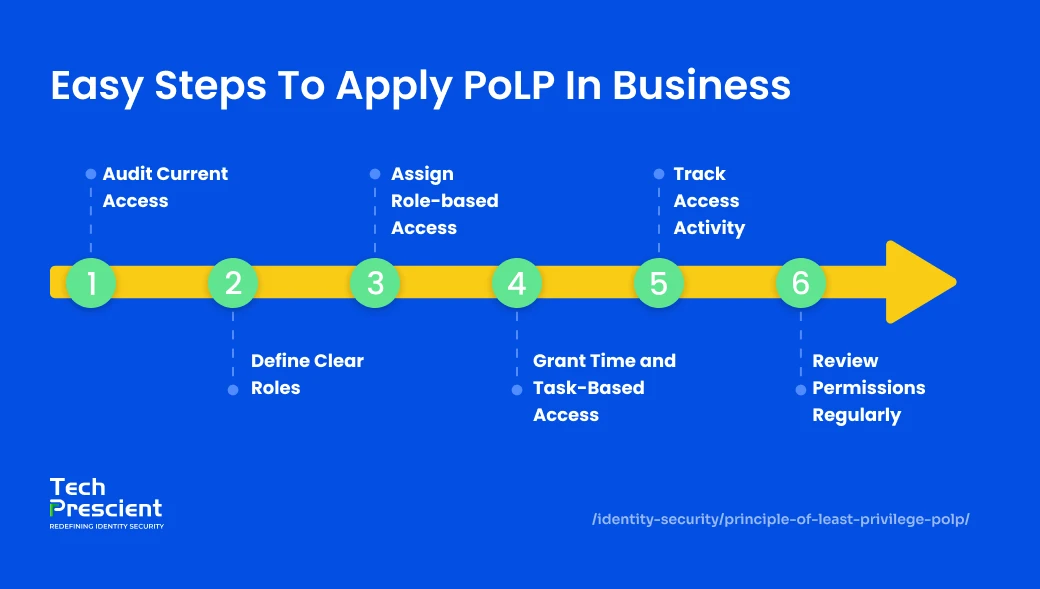
How to implement the Principle of Least Privilege:
- Audit existing user and system permissions
- Define role-based access policies
- Use Just-In-Time (JIT) access for temporary needs
- Automate access reviews and revocation
Often, you’ll find outdated permissions or blanket access that no longer align with roles.
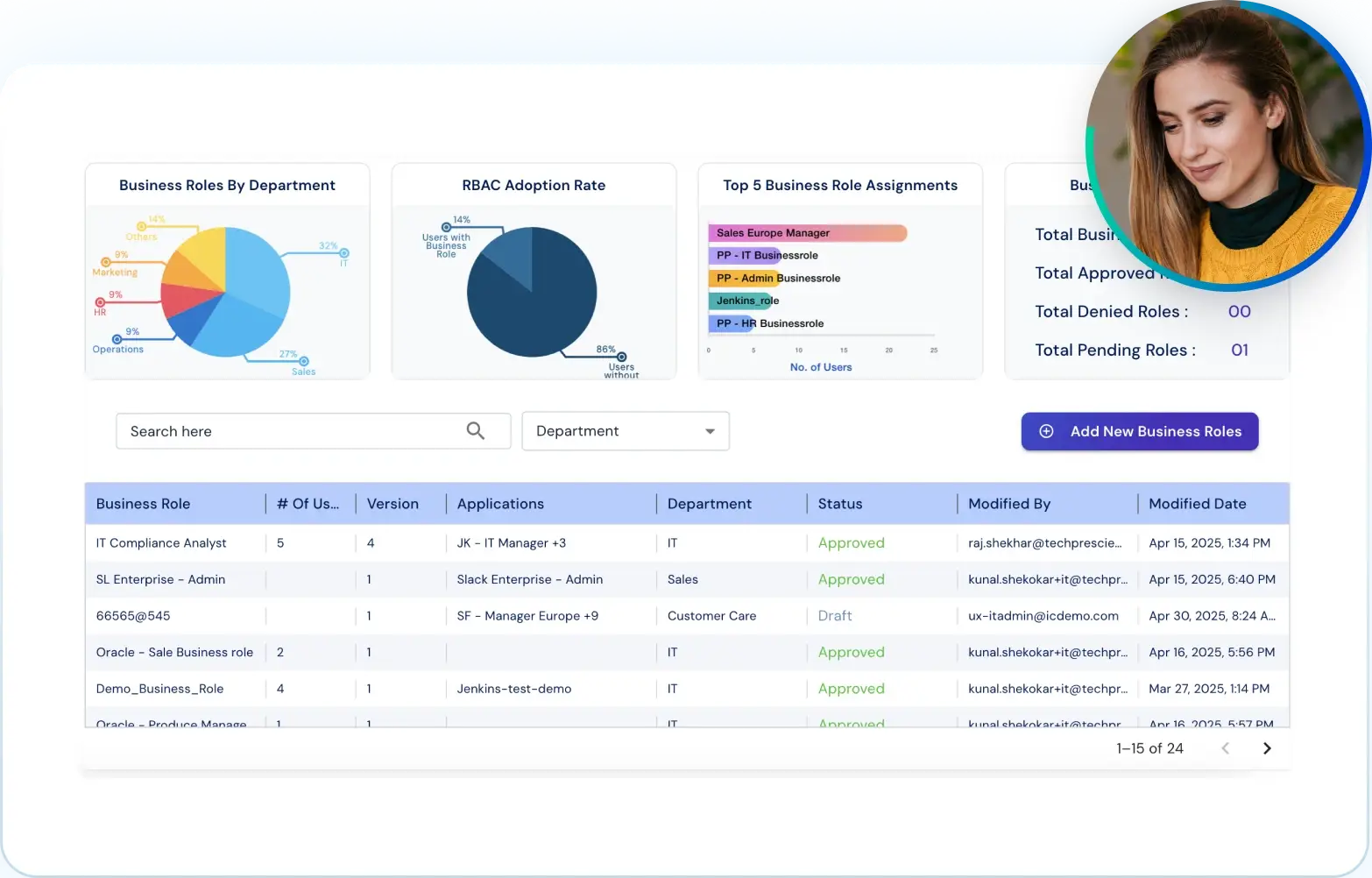
Once that baseline is established, define clear access roles using the principle of "need to know." Group similar access requirements under Role-Based Access Control (RBAC), so that permissions are assigned by responsibility, not person.
In fast-changing environments, Just-In-Time (JIT) access makes a difference. Temporary access can be granted for specific tasks or projects, then automatically revoked. This keeps access clean without slowing anyone down.
Finally, log all access events and conduct regular reviews. Automated tools can flag anomalies, reduce manual workload, and ensure the right people always have the right access, nothing more.
Understanding the least privilege conceptually is only half the work. The real challenge is applying it consistently across users, systems, and cloud environments.
Get a checklist for implementing the Principle of Least Privilege
A practical checklist to help security, IT, and compliance teams apply least privilege across identities, applications, and cloud infrastructure.

Common Challenges and How to Overcome Them
Implementing least privilege in an organization isn’t always straightforward. Legacy systems often weren’t built with fine-grained access control in mind, making integration difficult. In environments with dozens of applications and platforms, mapping out the exact access needs of each role can quickly become overwhelming.
Organizational resistance is another common challenge. Teams accustomed to broad access may perceive least privilege controls as restrictive without clear communication and policy alignment. Without strong communication and clear policies, these transitions can feel like a step backward. To address these challenges, organizations should combine policy updates with training, use automation tools to simplify access reviews and take a phased approach to implementation.
- Old systems: Hard to limit access if the tools don’t support it.
- Too many tools: Complex setups make access harder to manage.
- People push back: Some may resist change if they’re used to open access.
Benefits of Least Privilege in an Enterprise Environment
Applying the Principle of Least Privilege doesn't just reduce risk; it improves the overall health and efficiency of your organization. By minimizing unnecessary access, companies can stop malware from spreading across systems if a breach occurs. Limiting permissions also reduces the chances of human error or insider threats causing major disruptions.
From a compliance standpoint, least privilege makes audit preparation much smoother. When access is well-documented and clearly justified, audits become less stressful and more transparent. Additionally, it prevents privilege creep, the gradual build-up of access rights over time, which is often a hidden source of security gaps.
For the IT team, PoLP translates into fewer support tickets, cleaner access logs, and more time to focus on strategic tasks. Applying least privilege improves operational resilience by reducing unnecessary access, simplifying audits, and strengthening governance across identities and systems.
- Controls the spread of malware by identifying the potential threat footprint and restricting its actions.
- Limits insider threat potential by limiting the potential for accidental or malicious misuse of information.
- Streamlines audit readiness by providing traceable, role-based access and use controls.
- Increases productivity by reducing risk and IT overhead associated with access.
- Strengthens governance and decreases security exceptions across the board.
Principle of Least Privilege in Cloud and Modern IT Environments
Today’s IT environments are complex, with users operating across cloud platforms, SaaS tools, and hybrid infrastructures. Least privilege plays a foundational role in this context.
In cloud-native systems, PoLP works through identity-based access controls that integrate with platforms like AWS, Azure, and GCP. These platforms allow policies to be applied dynamically, depending on the user’s role, time of access, or even location.
Automation and alerts further support the model, enabling real-time responses to abnormal access behavior. For DevOps teams, limiting access to container configurations or deployment pipelines prevents costly errors or malicious changes.
In essence, PoLP scales with modern infrastructure when supported by the right identity governance and monitoring tools.
- Works with identity-based access
- Pairs well with automation and alerts
- Used in cloud, DevOps, and SaaS environments.
PoLP and Compliance
Organizations in regulated industries must adhere to strict compliance standards and PoLP directly supports these requirements by ensuring access is both minimal and auditable.
HIPAA: The Health Insurance Portability and Accountability Act mandates that healthcare data access is strictly limited to authorized individuals. PoLP helps organizations implement role-based access for patient records, reducing the risk of unauthorized exposure.
SOX: Under the Sarbanes-Oxley Act, organizations must maintain detailed logs showing who accessed financial systems and when. PoLP ensures access to financial data is tightly controlled and traceable, supporting both integrity and accountability.
GDPR: The General Data Protection Regulation enforces strict guidelines on data minimization and access control. PoLP aligns with GDPR by limiting access to personal data based on role and need, ensuring that only authorized personnel can handle sensitive information.
By embedding least privilege principles into access control policies, companies not only improve security but also simplify their path to regulatory compliance.
Simplify User Access with Identity Confluence
The Principle of Least Privilege isn’t just a technical best practice; it’s a mindset shift toward smarter, safer access. By giving people only what they need, when they need it, organizations can reduce risk, simplify audits, and build a stronger foundation for long-term security and compliance.
If your team is still managing access manually or using outdated controls, Organizations relying on manual or static access controls should evaluate whether their current approach aligns with modern identity and cloud security requirements.
Get the Least Privilege Checklist
Use our quick checklist to secure users, apps, and cloud access.

FAQs
It happens when users gradually accumulate access permissions they no longer need. Over time, this can create serious security vulnerabilities, as excessive privileges increase the likelihood of data breaches or internal misuse. Regular access reviews help reduce this risk.
Access rights should be reviewed on a quarterly basis or when there are major changes to their role. Regular reviews are important to validate that users only have the access they require at the moment, and to deter privilege creep.
Not if implemented correctly. Principle of least privilege (PoLP), with automation and role-based access control, not only allows users to get what they need promptly, but does so by mitigating the risks associated with open-ended access.
PoLP is important because many modern attacks start with someone having too many rights. By ensuring that users have the rights they need and nothing more, organizations are minimizing the chance of internal misuse and external compromise. PoLP is a first line of defense in cloud, hybrid, and remote-first enterprises.
Absolutely. PoLP is not only for users, but it also applies to applications, scripts, APIs, and service accounts, too. Every digital identity in your environment should follow least privilege principles to help limit unintended consequences.
The most common mistake is treating it as a one-time setup. In reality, PoLP is a continuous monitoring, review, and updating process to account for changes in user roles, applications and risk levels.
The principle of least privilege (PoLP) is often implemented in cloud environments through identity-based access or authentication control, policy automation and real-time monitoring capabilities. Role-Based Access Control (RBAC), Attribute-Based Access Control (ABAC), and Just-in-Time (JIT) access are all core components of effective cloud-based PoLP implementation.
Start by auditing your current access permissions. Map those permissions to job functions, get rid of the excess access based on that data, and define permissions that are role-based. This helps eliminate over-privileged user issues, and tools like Tech Prescient's Identity Confluence provide automated help with governance workflows.
It means users and systems should only have access to the resources required to perform their job duties, reducing security risks caused by excessive permissions.