Identity Governance Best Practices for 2026: Cloud, AI & Compliance-Ready IGA
Learn modern identity governance best practices for 2026, including cloud IGA, AI-driven automation, compliance, and replacing legacy tools.
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Last Updated date: April 28, 2026
Identity Governance and Administration (IGA) has become a foundational control in modern security architectures. In digital environments where access defines exposure, identity now represents the primary control point and a primary attack surface. Protecting access is no longer a secondary concern; it is central to securing applications, data, and infrastructure.
IGA directly addresses this shift. It is not a back-office workflow or a compliance checkbox. When implemented effectively, it provides a structured, scalable approach to defining who has access to which resources, under what conditions, and for what purpose across the organization.
By 2026, identity governance must move beyond manual controls and legacy tools. Cloud-first architectures, increasingly automated access decisions, and expanding regulatory requirements demand IGA practices that are designed to scale securely and adapt to continuous change.
The need for this evolution is well established. According to Varonis, more than 25% of security breaches originate from web applications, with stolen credentials remaining one of the most common entry points. Even capable IGA platforms can fall short if they are deployed without clear strategy and operational discipline. The following best practices are based on real-world implementations and are intended to help organizations move beyond baseline governance toward identity controls that function reliably in day-to-day operations, not just in policy documentation.

Key Takeaways:
- Identity and governance administration is crucial for managing access in today’s complex, high-risk business environment.
- Manual, error-prone access controls are the key concerns in traditional IGA frameworks.
- Modern IGA best practices focus on cloud scalability, AI-powered automation, and continuous compliance.
- IGA best practices, like Zero Trust and RBAC, strengthen security, reduce risk, and ensure policy-aligned access.
- An integrated and AI-powered IGA platform simplifies access management, ensures compliance, and unifies identity control across systems.
Identity Governance Maturity Assessment for 2026
Not sure how mature your IGA really is? Take the IGA Maturity Assessment.
Why Best Practices in IGA Matter in 2026
Organizations continue to integrate an expanding set of cloud platforms, applications, and identity systems to support business agility. While this consolidation improves operational efficiency, it also increases the complexity of managing access and expands the potential attack surface. Without disciplined governance, identity sprawl becomes difficult to control and even harder to audit.
Many enterprises already have an Identity Governance and Administration (IGA) framework in place. However, the effectiveness of that framework depends on how consistently best practices are applied. Proper implementation ensures that access policies are enforced as designed, risks are continuously evaluated, and compliance obligations are met without manual intervention.
IGA best practices are increasingly critical due to several converging factors:
-
Growth of identity-centric attacks: Credential theft, privilege escalation, and insider misuse now account for a significant portion of security incidents, requiring stronger controls around access provisioning and oversight.
-
Stricter regulatory expectations: Modern compliance frameworks demand granular access controls, auditable decision-making, and continuous visibility into user entitlements.
-
Automation and AI at enterprise scale: AI-driven governance can improve decision speed and detection accuracy, but only when grounded in well-defined policies and data structures.
-
Tool proliferation without governance discipline: Advanced IGA platforms alone do not reduce risk; without a clear strategy and operational best practices, they often fail to deliver measurable security outcomes.
Applying IGA best practices establishes a stable foundation for scaling identity operations while maintaining security, audit readiness, and policy integrity as technologies and threat models continue to evolve.
How to Replace Outdated Identity Governance Tools
Replacing outdated identity governance tools requires more than incremental upgrades. Modern environments demand automation, cloud-native architecture, and continuous risk evaluation to reduce manual overhead and close governance gaps that legacy platforms leave behind.
Many organizations still operate legacy IGA solutions that were not designed for cloud scale, hybrid architectures, or dynamic access patterns. These platforms often depend on manual workflows, lack reliable integrations, and provide limited real-time visibility into entitlements, creating operational friction and audit exposure.
Effective replacement of legacy IGA tools should be guided by the following best practices:
- Identify automation gaps across the access lifecycle: Evaluate where provisioning, deprovisioning, and access reviews still rely on manual processes that introduce delay or error.
- Adopt cloud-native, API-first integration models: Ensure the platform integrates seamlessly with HR systems, IAM, PAM, and SaaS applications to support end-to-end identity governance.
- Incorporate AI-driven risk analytics: Use contextual risk signals to improve access decisions, prioritize reviews, and detect anomalous entitlements.
- Enforce least privilege with continuous visibility: Move beyond periodic reviews by maintaining real-time insight into access rights and policy adherence.
Replacing legacy IGA tools with a modern, automation-driven approach enables organizations to scale identity governance securely while improving audit readiness and operational efficiency.
7 Best Practices for Identity Governance and Administration

The identity access control best practices ensure appropriate access controls, detect malicious user behavior, protect sensitive data, and ensure compliance. So, let us have a look at seven essential identity governance and administration best practices to implement effective data access governance.
Executive Sponsorship & Governance Alignment
One of the IGA best practices is aligning executive stakeholders who will actively participate in the identity governance. Executives or leaders from IT, HR, legal, compliance, and senior management are usually a part of this process. Executive sponsorship ensures accountability and drives cross-functional collaboration, and helps align the IGA strategy with organizational goals and compliance requirements.
To support this alignment, it is important to first have a clear understanding of the organization’s objectives. It can be enhancing data security or meeting the industry-specific regulatory standards. It is necessary to know the specific regulatory frameworks that apply to your business. Then, you can effectively design the policies and processes for identity lifecycle management.
Pro Tip
IGA programs fail more often due to lack of ownership than lack of tools. Assign a single executive sponsor accountable for outcomes, not just approvals.
Adopt a Zero Trust Security Model
Zero trust is a security framework that is based on the principle of never trust, always verify. This means no device, user, or application should be inherently trusted. Every individual and device should be strictly verified and validated before giving access to the organization’s data, applications, or network.
Identity is one of the five core pillars of the zero-trust security framework. The others are network, devices, applications and workloads, and data.
To strengthen identity verification in zero trust, organizations should invest in identity and access management solutions (IAM), single sign-on (SSO), and multi-factor authentication. As IGA best practices, implement the least access privilege and role-based access controls.
- Least access privilege means that users and devices have access to only those applications and resources that are necessary to perform their duties.
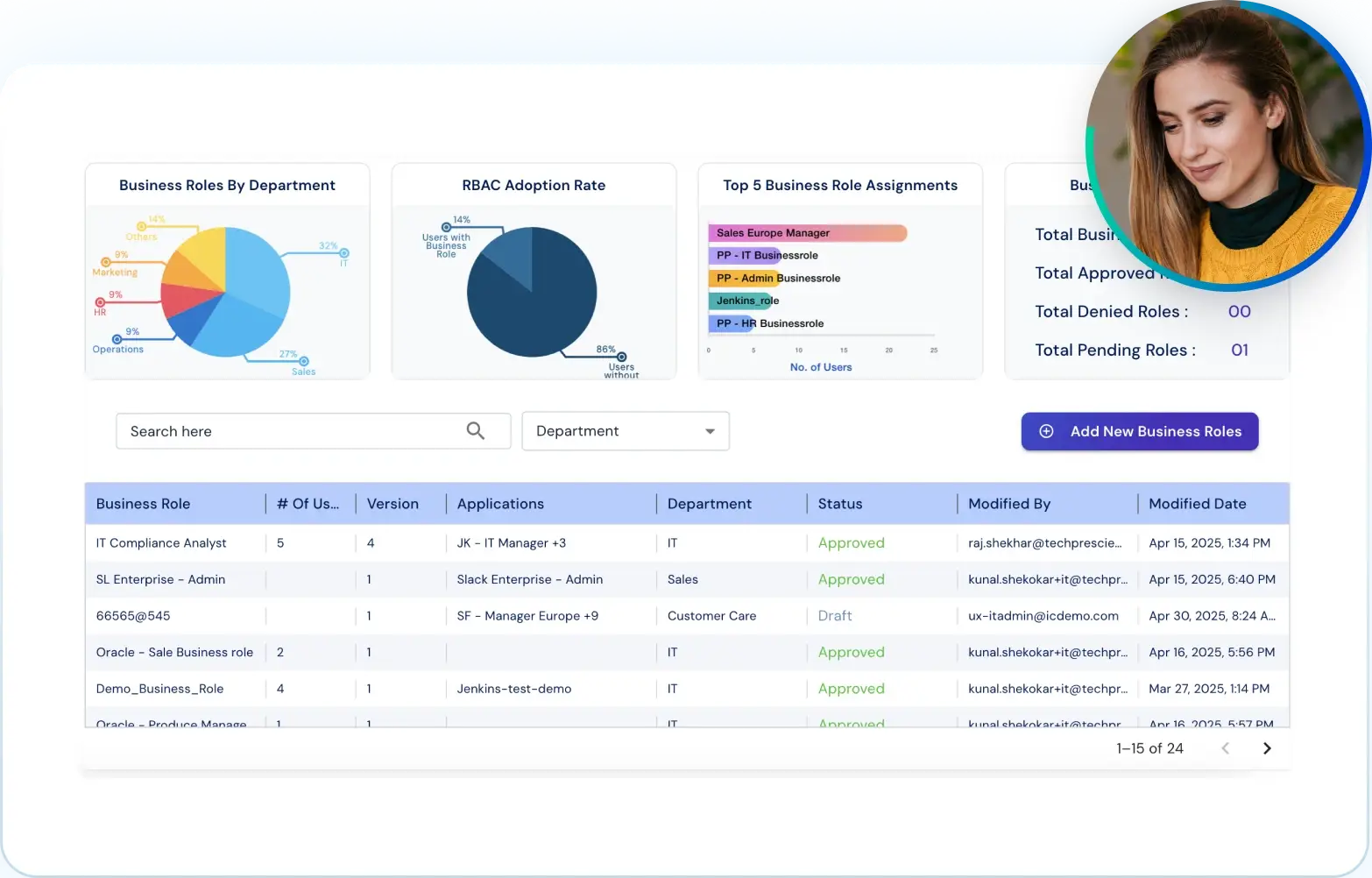
- The role-based access control (RBAC) is a methodology that restricts system access on the basis of an employee’s role in the organization.
RBAC complements the principle of least privilege by providing a structured way to manage access rights at scale. With a centralized zero-trust system in place, you don’t need to hire as many people for managing, monitoring, securing, refining, and updating security controls.
Enforce Access Reviews & Recertifications
Periodic access reviews are essential to ensure that users still need the permissions they currently hold. Employees may leave the organization, change departments, or take on new responsibilities. In large enterprises, these changes can affect hundreds of user accounts.
Regular access reviews become a part of a broader cyber hygiene program. It helps in ensuring that permissions are accurate, appropriate, and aligned with current roles. With regular access reviews, organizations can remove excessive or outdated privileges, detect orphan accounts, revoke access for inactive users, and strengthen their overall security posture.
Additionally, access reviews are not just identity access control best practice; they are a compliance requirement under regulations such as Sarbanes-Oxley (SOX), PCI DSS, HIPAA, and GDPR. Failure to conduct them properly can expose the organization to legal and financial risks.
Common Pitfall
Treating access reviews as a quarterly checkbox instead of a risk-based decision process leads to approval fatigue, and missed threats.
Implement Role-Based Access Control (RBAC)
Role-based access control, or RBAC, is an access management approach where minimum access provisions are assigned to employees on the basis of their job roles. This restricts access to only pre-defined role privileges.
It is one of the identity access control best practices as it eliminates the need to provision every user with a customized set of user permissions. RBAC defines every role and determines the access rights to each role. This makes it easier for organizations to onboard and offboard employees, update job functions, and transform business operations.
The RBAC system needs to follow three basic rules:
- Role assignment: Every user must assign at least one active role to exercise permissions and privileges.
- Role authorization: The user must be authorized to take the roles that are assigned.
- Permission authorization: Permissions or privileges are allowed only to the users who have been authorized through their role assignment.
An identity and access management solution can help in implementing both authorization and authentication required by RBAC. IAM systems can verify a user’s identity by checking their credentials in a centralized database. Then, after authentication, the system can check their role and grant the permissions as defined in the RBAC scheme.
Enable Just-in-Time (JIT) Access
Just-in-time access is another identity access control practice in which the users are provided temporary, time-bound access to specific systems, applications, or data, only when it’s needed and only for as long as necessary.
This is an IGA framework best practice as it helps in eliminating the risks associated with standing privileges. To implement Just-in-Time access, you first need to analyze the high-risk accounts or systems. This may include third-party contractor access, high-valued accounts (sysadmins, domain admins, etc), and DevOps.
You can deploy a privilege access management (PAM) solution that has JIT capabilities, like temporary privilege elevation and session-based access with automatic revocation. Now, JIT prioritizes how long the user has access to a certain resource. So, the shorter the time window, the better the security.
However, this shouldn't be applied as a rigid rule. Setting access durations too short may interrupt users before they can complete their tasks. The key is to balance security with productivity by defining time limits based on the nature of the task, risk level, and user role.
Identity Governance Maturity Assessment for 2026
Not sure how mature your IGA really is? Take the IGA Maturity Assessment.
Automate Identity Lifecycle Management
Manually handling all the identity and access management processes becomes tedious and overwhelming as the business organization scales. Besides, the risk of errors and delays increases significantly, leading to security gaps, compliance issues, and poor user experience.
That’s why, as one of the identity governance best practices, automate the identity lifecycle management, from onboarding and access provisioning to role changes and off-boarding. This will streamline the process end-to-end, reduce administrative overhead, and ensure that all the requests related to identity access are resolved at the earliest.
With automation, users receive timely and appropriate access based on their current roles and responsibilities. It also ensures that access is revoked immediately when it's no longer needed, reducing the attack surface.
Monitor with Risk Analytics & Alerts
Continuous monitoring is the cornerstone for effective identity and access management. As an identity access control best practice, you need to shift from reactive to proactive identity governance strategy. By using risk analytics and real-time alerts, organizations can identify unusual behaviors, policy violations, or suspicious access patterns before they escalate into breaches.
Best Practices for Cloud Identity Governance at Scale
Cloud identity governance must support scale, automation, and continuous enforcement across SaaS, IaaS, and hybrid environments. As organizations migrate workloads to the cloud, identity sprawl accelerates, increasing the risk of excessive permissions, orphaned accounts, and inconsistent policy application.
Effective cloud IGA practices are designed to maintain governance without introducing friction that slows delivery or adoption. This requires moving beyond static controls and periodic reviews toward continuous, policy-driven oversight aligned with how cloud environments operate.
Identity Governance Maturity Assessment for 2026
Not sure how mature your IGA really is? Take the IGA Maturity Assessment.
Key best practices for cloud identity governance include:
- Centralized governance across cloud and SaaS environments: Maintain a unified governance layer that enforces consistent access policies across multiple cloud providers and software-as-a-service platforms.
- Automated provisioning driven by authoritative identity sources: Use HR and lifecycle signals to provision and revoke access automatically as roles change.
- Continuous access evaluation: Replace point-in-time audits with ongoing access assessments to identify risk as it emerges.
- Real-time policy enforcement: Apply least-privilege and segregation-of-duties controls dynamically across cloud resources.
Adopting these practices allows organizations to scale cloud identity governance while preserving visibility, control, and compliance as environments continue to evolve.
Cloud Governance Gotcha
Native cloud IAM tools manage access, but not governance. Without centralized IGA, policy enforcement becomes inconsistent across platforms.
Best Practices for Using AI in Identity Governance
Artificial intelligence can improve identity governance by increasing decision accuracy, reducing manual effort, and surfacing risk that traditional rule-based approaches often miss. However, AI is most effective when applied within a clearly defined governance framework rather than treated as a standalone capability.
When properly implemented, AI enables organizations to move from reactive access reviews to continuous, risk-aware governance. This shift depends on using AI to augment policy enforcement and analyst judgment, not replace them.
Effective AI-driven identity governance practices include:
- Anomaly detection based on access behavior: Apply machine learning models to identify unusual access patterns, privilege accumulation, or deviations from established baselines.
- Risk-based access certifications: Prioritize access reviews using contextual risk signals instead of relying on static, time-based certification cycles.
- Predictive insights for entitlement cleanup: Use historical access data and usage patterns to identify unused or high-risk entitlements before they become audit issues.
- Intelligent recommendations to reduce manual workflows: Support approvers with data-driven recommendations to streamline decisions while maintaining accountability.
Applying AI in this structured manner strengthens identity governance outcomes by improving visibility, focusing effort on meaningful risk, and maintaining policy integrity at scale.
How to Choose the Right IGA Solution for SOX and GDPR
Selecting an Identity Governance and Administration (IGA) solution for SOX and GDPR compliance requires a focus on control effectiveness, audit traceability, and consistency of enforcement. Compliance outcomes depend less on policy intent and more on whether access decisions can be validated, reviewed, and reproduced under audit scrutiny.
When evaluating IGA platforms for regulatory compliance, organizations should prioritize capabilities that support continuous governance and defensible reporting rather than manual evidence collection or point-in-time reviews.
Key evaluation criteria include:
- Automated evidence collection and audit-ready reporting: The platform should generate complete, time-stamped records of access decisions, approvals, and changes without relying on manual documentation.
- Segregation of duties (SoD) enforcement: Built-in SoD controls must detect and prevent conflicting access both at provisioning time and as roles evolve.
- Role lifecycle governance and certification workflows: Support for role definition, modification, and periodic access certification is essential to demonstrate ongoing control over entitlements.
- Alignment with GDPR access principles: The solution should enforce least-privilege access, support transparency into user permissions, and enable timely access removal in response to data subject or role changes.
An IGA platform that meets these requirements enables organizations to demonstrate sustained compliance with SOX and GDPR while reducing audit friction and operational risk.
Identity Governance Maturity Assessment for 2026
Not sure how mature your IGA really is? Take the IGA Maturity Assessment.
IGA Solution Makes Best Practice Easy
Adopting an IGA platform is not a one-time implementation effort. Its value depends on how effectively it is configured and operated over time. A well-designed IGA solution provides the structure needed to define, enforce, and automate standardized processes across user provisioning, access reviews, policy enforcement, and identity lifecycle management.
Best practices ensure that these capabilities are applied consistently and at scale. When governance processes are clearly defined and automated, organizations reduce reliance on manual intervention, limit excessive or unnecessary access, and maintain accurate access records across systems.
Applied correctly, an IGA platform improves operational efficiency, reduces human error, and strengthens audit readiness by making access decisions repeatable, traceable, and policy-driven.
Final Thoughts
Identity governance and administration is no longer just a compliance requirement. It is a core security function that determines how effectively organizations control access, reduce identity risk, and protect critical systems and data.
As cloud, hybrid, and SaaS environments grow, identities and entitlements multiply. Without strong IGA best practices, organizations face increased risk from over-permissioned users, delayed access removal, and limited visibility. Modern IGA programs must prioritize automation, least privilege, and continuous access governance.
By combining proven identity governance practices with AI-driven automation, organizations can simplify access management, strengthen compliance, and reduce identity-based risk at scale. To see how Tech Prescient supports modern identity governance
FAQs
Enforcing the principle of least privilege is foundational to effective identity governance. Users should be granted only the access required to perform their job functions, and that access should be continuously evaluated. This limits exposure from compromised credentials, insider misuse, and role drift over time.
At a minimum, access reviews should be conducted quarterly. Organizations operating in highly regulated or high-risk environments may require monthly or continuous reviews. Review frequency should be determined by risk tolerance, regulatory obligations, and the sensitivity of accessed systems and data.
Yes, small businesses can adopt IGA best practices using cloud-based solutions that offer scalable features, automation, and compliance tools without the high upfront costs of traditional enterprise systems.
IAM (Identity and Access Management) best practices focus on managing user identities and access controls, like authentication and authorization. IGA framework best practices go further, adding oversight, compliance, role management, and access certification to ensure governance and reduce audit risk.
Automation enhances IGA by streamlining user provisioning, access reviews, policy enforcement, and audit reporting. It reduces human error, accelerates response times, and ensures consistent compliance across systems.