What Is Zero Trust Security? Principles, Model & Examples
Explore Zero Trust Security: what it is, why it matters, key principles, and best practices to protect modern enterprises from internal and external threats.
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Last Updated date: April 7, 2026
Zero Trust Security is a cybersecurity model that is built on the principle of “never trust, always verify,” meaning no user, device, or application should be trusted by default. Every access request is continuously verified using identity, device posture, and contextual signals to prevent unauthorized access, data breaches, and lateral movement within systems.
Traditional perimeter-based security no longer works in today’s cloud-first, remote, and SaaS-driven environments. Zero Trust Security replaces implicit trust with continuous verification, ensuring that every user, device, and access request is validated in real time. Instead of relying on network boundaries, Zero Trust focuses on identity, context, and least-privilege access to reduce breach impact and improve security resilience.
Key Takeaways:
- Zero Trust Security follows the principle of “never trust, always verify.”
- Every access request is authenticated using identity, device health, and risk signals.
- It minimizes lateral movement and reduces the attack surface.
- Core principles include least privilege, continuous authentication, and microsegmentation.
- Zero Trust is critical for securing cloud apps, remote users, and third-party access in 2025.
What Is Zero Trust Security?
Zero Trust Security is a modern cybersecurity framework designed to eliminate implicit trust from digital environments. Unlike traditional security models that automatically trust users or devices inside the network, Zero Trust treats every access request as potentially risky and verifies it continuously.
Whether a user is accessing systems from inside the office, remotely, or via third-party tools, Zero Trust requires strict identity verification, device validation, and contextual analysis before granting access.
Technologies such as Zero Trust Network Access (ZTNA), continuous authentication, identity-based access control, and microsegmentation work together to ensure users can only access the specific resources they are authorized for.
Zero Trust is not a single tool; it is an architectural approach that helps organizations protect systems, data, and identities across hybrid and cloud environments.

Why Zero Trust Matters in 2026
In 2026, organizations face an expanded attack surface driven by cloud adoption, remote work, SaaS sprawl, and third-party integrations. Zero Trust matters because it removes outdated assumptions about trusted networks and enforces security at every access point.
By continuously verifying identities and devices, Zero Trust helps organizations prevent credential-based attacks, limit breach impact, and meet evolving compliance requirements. It enables consistent access control across hybrid environments while supporting innovation without sacrificing security.
As threats and technologies continue to evolve, Zero Trust offers a flexible and forward-looking way to stay secure.
- In 2026, organizations operate across cloud, hybrid, and SaaS environments that significantly expand the attack surface. Zero Trust matters because it removes reliance on network-based trust and enforces security decisions at every access point.
- By continuously verifying identities, devices, and contextual risk, Zero Trust helps organizations reduce credential misuse, limit lateral movement, and contain breaches more effectively. It also supports consistent policy enforcement across distributed environments while aligning with evolving regulatory and compliance requirements.
- Rather than relying on perimeter defenses that fail once breached, Zero Trust provides a structured, resilient approach to access control that scales with modern infrastructure and emerging threat techniques.
Core Principles of Zero Trust Architecture
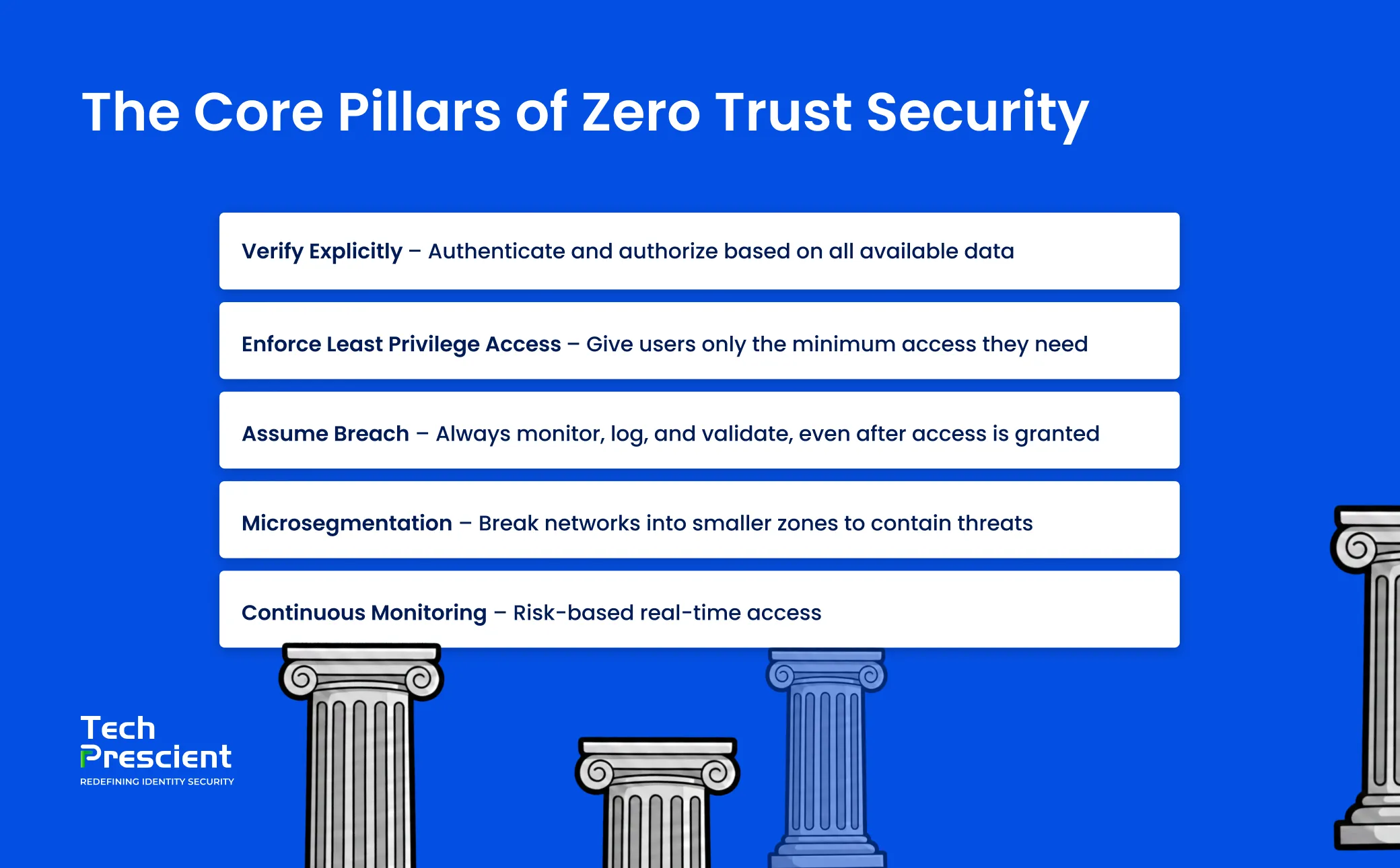
The Zero Trust security model is built on five core principles that ensure access is continuously validated, tightly controlled, and monitored across all users, devices, and systems.
1. Verify Explicitly
Every access request must be authenticated and authorized based on real-time data. This includes user identity, location, device health, and even behavioral context. Zero Trust replaces blind trust with data-backed decisions.
To implement this, organizations should use tools like multi-factor authentication (MFA), single sign-on (SSO), and robust identity and access management (IAM) systems. These solutions help validate both human and non-human identities, ensuring that access is never based on assumptions.
2. Enforce Least Privilege Access
No user should have more access than they actually need. This is known as the least privilege principle, and it plays a critical role in limiting the potential damage from a compromised account.
Whether it's a senior executive or a temporary contractor, access should be tailored to their specific role and responsibilities. Fine-grained access control ensures users can access only the applications and data required for their role.
Is Your Zero Trust Strategy Actually Working?
Validate your readiness and turn principles into execution
3. Assume Breach
Zero Trust assumes that breaches are inevitable, so it is built to contain and minimize their impact. Even after access is granted, systems should log activity, validate user behavior, and monitor for any signs of malicious intent.
By shifting from a reactive to a proactive security posture, organizations can detect unusual patterns early and respond faster to threats. This principle aligns closely with continuous authentication and real-time risk assessment.
4. Microsegmentation
Microsegmentation involves dividing the network into smaller zones so that even if a threat actor gets in, they cannot move freely across systems. Each zone has its own set of access rules, making lateral movement significantly harder for attackers.
By isolating workloads and applications, microsegmentation adds a powerful layer of defense and limits the exposure of critical assets.
5. Continuous Monitoring
Security in a Zero Trust environment is not a one-time check. It requires continuous monitoring of user activity, device posture, and network traffic. This includes using tools for behavioral analytics, risk scoring, and real-time alerting.
With a strong monitoring system in place, organizations can adapt access controls instantly and block suspicious activity before it becomes a threat.
What Is the Best Way to Eliminate Implicit Trust in Identity Systems?
The most effective way to eliminate implicit trust in identity systems is by adopting a Zero Trust security model that enforces identity-based access, least privilege, and continuous verification.
Instead of granting blanket access based on network location, Zero Trust validates users and devices at every interaction. This approach ensures that trust is never assumed and access is always earned based on real-time risk and context.
Zero Trust vs Traditional Security Models
The shift from perimeter-based security to Zero Trust architecture marks a major change in how organizations approach cybersecurity. While traditional models focus on building a strong outer defense, they often fail once that perimeter is breached. Zero Trust, on the other hand, is built on the assumption that threats can come from anywhere inside or outside the network.
| Feature | Traditional Perimeter Security | Zero Trust Security Model |
|---|---|---|
| Trust Model | Trust is granted to users inside the network | No implicit trust. Every request must be verified |
| Network Perimeter | Strong focus on securing the outer boundary | Perimeter is irrelevant. Focus is on identity and context |
| Access Control | Broad access within the network once a user is inside | Strict identity-based access for each application or resource |
| User Verification | One-time authentication at login | Continuous verification of identity, device, and context |
| Lateral Movement Risk | High. Once inside, attackers can move across systems | Minimal. Microsegmentation and access control limit lateral movement |
| Response to Breach | Reactive. Focus on detecting after the breach | Proactive. Designed to limit breach impact from the start |
| Visibility and Monitoring | Limited visibility across all users and devices | Comprehensive visibility and real-time monitoring of all access attempts |
| Device Trust | Often not verified after initial login | Ongoing checks for device health and posture |
| Data Protection | Data is protected primarily at the perimeter | Data is protected at every access point and user interaction |
| Scalability in Cloud Environments | Struggles to adapt to hybrid and multi-cloud setups | Built to support cloud-native, hybrid, and remote environments |
Not sure how close your organization really is to Zero Trust?
Assess your Zero Trust maturity and get a clear 90-day plan
Zero Trust Use Cases
As organizations continue to adapt to hybrid work models, cloud-first strategies, and growing digital ecosystems, Zero Trust security offers practical solutions to some of the most pressing cybersecurity challenges. Its flexible design allows it to be implemented across multiple environments and industries, making it an essential part of a modern security framework.
Here are some of the most impactful use cases where Zero Trust helps organizations strengthen their security posture:
1. Remote Workforce Access to Sensitive Applications
With employees working from various locations and devices, traditional perimeter security fails to offer adequate protection. Zero Trust network access (ZTNA) ensures that only verified users and trusted devices can access specific business applications, regardless of where they are connecting from. This reduces unauthorized access risks and secures corporate data across distributed teams.
2. Privileged Access Control
Accounts with elevated access are prime targets for cyber attackers. Zero Trust enforces strict verification for all privileged actions, ensuring that even admin-level users are granted access only after continuous identity and context checks. By applying the least privilege principle, it limits what users can access and what actions they can take, reducing the blast radius in case of compromise.
3. Securing Cloud Environments
As workloads and data shift to the cloud, consistent and adaptive access controls become essential. Zero Trust architecture protects multi-cloud and hybrid environments by verifying every access request and enforcing identity-based policies. This prevents unauthorized lateral movement and keeps cloud resources secure at all times.
4. Protection from Ransomware and Insider Threats
Zero Trust helps mitigate the risk of ransomware attacks by restricting access paths and monitoring user behavior in real time. It also reduces the potential for insider threats by ensuring users can only interact with the data and systems necessary for their roles. Microsegmentation and continuous authentication add extra layers of control, helping detect and block suspicious activity before it escalates.
5. Third-Party and Vendor Access Management
Vendors, contractors, and third-party collaborators often need temporary or limited access to internal systems. Zero Trust enables organizations to manage these connections securely by creating time-bound, role-specific access policies. Every access attempt is logged and monitored, providing transparency and control without sacrificing productivity.
How Do You Verify Every Access Request in Real Time?
In a Zero Trust security model, every access request is verified in real time using multiple contextual signals, including:
- Strong identity verification through MFA and SSO
- Device posture checks, such as OS health and security status
- Risk-based authentication using behaviour and location
- Continuous authentication that reassesses trust throughout the session
This ensures access decisions are dynamic, adaptive, and resistant to credential misuse or insider threats.
Steps to Implement Zero Trust in Your Organization
Adopting a Zero Trust security model requires more than just new tools; it demands a shift in how access, users, and data are managed across the enterprise. The process is not one-size-fits-all, but following a structured roadmap can help organizations implement Zero Trust effectively and efficiently. Here are the key steps to guide your Zero Trust implementation:
1. Identify Critical Assets and Users
Start by creating an inventory of all digital assets, including cloud applications, on-premise systems, user groups, and data repositories. Determine which assets are most sensitive or business-critical and identify the users who interact with them. Understanding what needs to be protected is the foundation of a Zero Trust approach.
2. Map Current Access Flows
Analyze how users, devices, and applications currently interact with systems and data. This includes identifying who accesses what, under what conditions, and from which locations or devices. Mapping these access flows helps detect risky patterns, control gaps, and potential areas for policy refinement.
3. Deploy Identity-Based Authentication (MFA, SSO)
Implement robust identity and access management (IAM) controls that verify users and devices before granting access. Use multi-factor authentication (MFA) to add another layer of security, and integrate single sign-on (SSO) to streamline and secure user access across applications. This ensures only verified identities gain access, based on contextual factors like device health and user behaviour.
4. Segment Networks and Isolate Resources
Use microsegmentation to divide your network into smaller, isolated zones with distinct access rules. By doing so, even if a threat actor breaches one segment, they are restricted from moving across the environment. Isolating high-value assets and applying specific security controls to each segment significantly limits the impact of any intrusion.
5. Monitor Continuously with Risk-Based Analytics Real-time visibility is key in a Zero Trust environment. Continuously monitor user activity, device posture, and network traffic using behavioural analytics and risk scoring. This enables adaptive access decisions and a rapid response to unusual behaviour. Constant monitoring helps detect potential threats early and strengthens the security posture over time.
Benefits of a Zero Trust Security Model
Implementing a Zero Trust security model offers far more than just improved threat protection. It brings measurable advantages across security, operations, and user experience, making it a strategic investment for modern organizations.
Here are the key benefits of adopting Zero Trust:
1. Reduces Lateral Movement
Zero Trust assumes that threats can exist anywhere, even inside the network. Enforcing identity-based access and isolating workloads, it limits how far an attacker can move if they gain entry. This containment significantly reduces the risk of a widespread breach.
2. Minimizes the Attack Surface
By granting access based on strict verification and least privilege, Zero Trust minimizes the number of entry points exposed to attackers. Microsegmentation and continuous validation help ensure that only the right users access the right resources at the right time—nothing more, nothing less.
3. Improves Compliance
Whether it’s GDPR, HIPAA, SOX, or PCI DSS, regulatory frameworks demand strong access control and data protection. Zero Trust aligns with these requirements by offering granular visibility, access logs, and automated policy enforcement. This simplifies audit readiness and supports long-term compliance.
4. Better Control Over SaaS and Third-Party Risks
Organizations rely heavily on third-party vendors and cloud applications. Zero Trust helps manage this complexity by enabling strict access controls for external users and ensuring that SaaS applications are only accessible to verified identities. This reduces the risk posed by unmanaged or loosely governed connections.
5. Supports Hybrid Workforce Securely
With employees working across locations, devices, and networks, consistent security is essential. Zero Trust makes it possible to secure hybrid work environments by verifying every access request in real time no matter where the user is. It improves the end-user experience while maintaining high levels of control and visibility.
Is Your Zero Trust Strategy Actually Working?
Validate your readiness and turn principles into execution
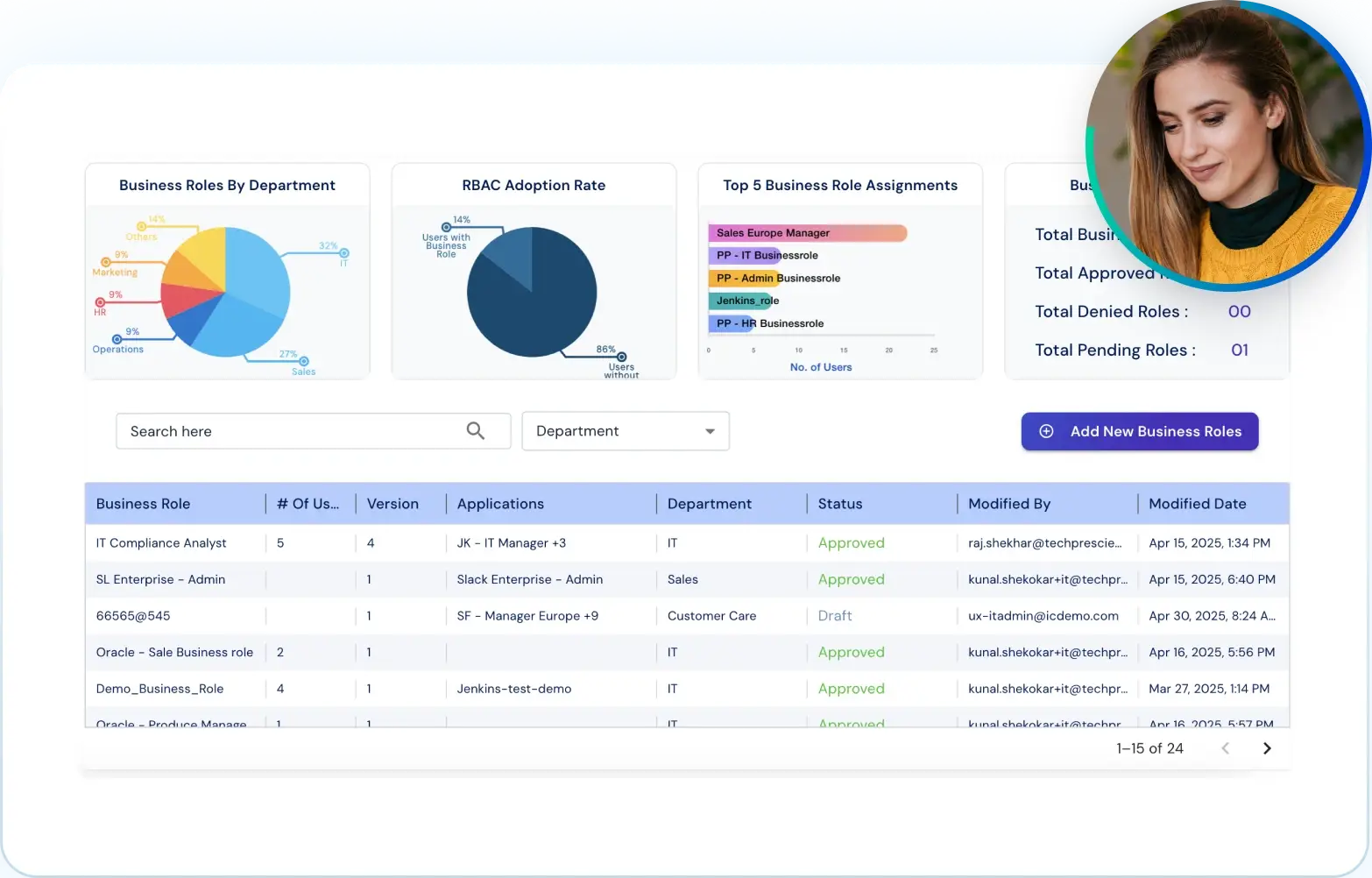
Our Approach to Zero Trust: Why Tech Prescient Solutions Work
Tech Prescient applies Zero Trust using an identity-first approach designed for modern cloud and hybrid environments. Access decisions are based on verified identity, device health, and real-time risk, not network location.
The platform combines identity-based access control, risk-aware authentication, microsegmentation, and continuous monitoring. This helps organizations reduce exposure, limit lateral movement, and maintain visibility across users, applications, and data as environments change.
See how the platform enforces real-time access control and visibility across users, applications, and data.
FAQs
Zero Trust Security is a model that assumes no user or device should be trusted automatically. Every access request is verified continuously using identity, device health, and contextual signals before access is granted.
The Zero Trust security model eliminates implicit trust and requires continuous authentication, least privilege access, and monitoring to protect systems from both external and internal threats.
Zero Trust limits insider threats by enforcing least privilege access, monitoring user behaviour, and verifying access in real time, preventing users from accessing resources beyond their role.
No. Zero Trust can be implemented by organizations of all sizes to secure cloud apps, remote workforces, and third-party access more effectively.