What Is Access Certification in Identity Governance & Why It Matters?
Access certification ensures users have the right access through periodic reviews. Learn the process, best practices & audit-ready compliance approach for 2026
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Last Updated date: April 30, 2026
Access certification is the process of periodically reviewing and validating user access rights to ensure they align with job roles, security policies, and compliance requirements. It helps organizations reduce insider risk, prevent privilege creep, and stay audit-ready.
Access certification is a security practice that involves periodically reviewing and validating user access rights to ensure they align with organizational policies, job roles, and business requirements. It is a critical component of Identity Governance and Administration (IGA), helping prevent unauthorized access, reduce breach risk, and meet regulatory standards such as SOX, HIPAA, and GDPR.
In a modern zero-trust environment, with increasing insider threats and strict compliance rules, access certification has moved from being just a good practice to a business necessity. In fact, by 2026, it’s projected that half of all cloud security failures will stem from inadequate identity, access, and privilege management, which highlights the need to regularly check internal access. If you are a compliance officer, IT leader, or business stakeholder, being able to check that only the right people have the right access and at the right time is crucial not just for security but also for business accountability.
Key Takeaways
- Access certification helps stop unauthorized access by reviewing user permissions regularly.
- It supports compliance with laws like SOX, HIPAA, and GDPR through scheduled access reviews.
- Automation reduces manual work and helps avoid reviewer fatigue.
- It enforces Zero Trust and the principle of least privilege, by checking and updating access as needed

What Is Access Certification?
Access certification is a structured process used in identity governance to review, validate, and attest user access permissions across systems, ensuring they remain appropriate, necessary, and compliant over time.
Rather than granting access indefinitely, access certification introduces structured accountability. It requires designated reviewers to confirm that permissions align with defined job responsibilities and current business need, and to revoke access when they do not. This ongoing validation is essential to maintaining security posture, data integrity, and regulatory compliance.
Think of it this way:
Access certification is like a recurring background check for permissions. Even if access was approved once, it must be re-verified as roles, risks, and business needs change.
Access certification focuses on the following key areas:
Access Review:
Access certification entails examining the permissions assigned to users to verify that they correspond with their roles and responsibilities within the organization. This helps safeguard systems by preventing unauthorized access and lowering the chances of data breaches.
Permission Validation:
It ensures that users hold only the necessary permissions to carry out their responsibilities effectively, without becoming overprivileged. It helps strike the right balance between maintaining strong security controls and enabling workplace productivity.
Issue Detection and Remediation:
The access certification process often reveals discrepancies or inconsistencies in how access rights are managed. Common issues include inappropriate access, orphaned accounts, and users with excessive privileges. Addressing these problems promptly is critical to ensuring a secure and well-governed IT environment.
Stakeholder Participation:
Key stakeholders such as application owners, managers, and compliance officers play an essential role in the access certification process. They are responsible for reviewing and approving access rights based on their understanding of user roles and the organization's security policies.
Compliance Assurance:
Access certification plays a critical role in meeting regulatory requirements and upholding industry standards for data security and privacy. Through regular validation of access rights, organizations can effectively demonstrate compliance during audits and assessments.
Why Access Certification Matters in 2026?
In 2025, access certification is essential due to hybrid work, cloud adoption, Zero Trust mandates, and stricter compliance requirements, helping organizations prevent access abuse and pass audits with confidence.
As organizations scale across SaaS platforms, cloud infrastructure, and distributed teams, access decisions made months earlier often remain unchecked. This creates conditions for privilege creep, orphaned accounts, and misaligned access, issues that are frequently identified during audits and investigations. Access certification provides the structured mechanism to prevent these risks through regular, documented review.
Responding to Zero Trust Demands
Zero Trust architecture is based on the principle that threats can emerge from both within and outside the network. It mandates ongoing verification of access rather than relying on one-time approvals. Access certification reinforces this approach by facilitating periodic and on-demand entitlement reviews, enabling the detection and removal of unauthorized or excessive access before it leads to potential security risks.
Enforcing Least Privilege at Scale
It is almost impossible to manage least privilege manually for a large number of users. Access certification platforms automate the process by routinely reviewing user access rights, confirming their necessity, and initiating revocation workflows when appropriate, ensuring that least privilege is consistently enforced and maintained across the organization.
Avoiding Audit Penalties
Regulatory compliance frameworks such as SOX, HIPAA, GDPR, and ISO 27001, along with recently introduced regulations like NIS2 and DORA, mandate continuous, periodic, and well-documented access reviews. Access certification plays a critical role in meeting these requirements by providing the necessary evidence during security audits. Failure to implement these controls can expose organizations to substantial financial penalties and reputational damage.
“Access reviews ensure the right people have the right access, nothing more, nothing less. It’s the foundation of trust and compliance.”
-Tech Prescient IAM Consultant

Core Elements of the Access Certification Process
The access certification process includes campaign setup, access reviews and recertification, and audit-ready logging to ensure timely, accurate, and compliant access decisions. A strong access certification strategy involves regular and well-organized review campaigns which has clear roles, defined review areas, and reports ready for the audits. These steps are crucial for timely reviews, which are useful for spotting risks and supporting compliance. Modern IGA platforms make this process easier by using automation, real-time monitoring, and alerts to manage the process smoothly.
Execution Tip:
Start with high-risk applications and privileged roles first. Trying to certify everything at once often leads to rushed approvals and reviewer fatigue.
Campaign Setup & Reviewer Roles
Effective access certification within an IGA platform depends on a structured campaign setup and the clear assignment of reviewer roles. The process begins by defining the campaign scope, identifying the specific users, entitlements, or applications that require review during a given cycle. Reviewers such as direct managers, application owners, or compliance officers are assigned based on their familiarity with and responsibility for the access in question.
These campaigns typically incorporate defined deadlines, automated reminders, escalation workflows for overdue tasks, and configurable review logic (such as direct certification, deny, or delegation). Modern IGA solutions enhance this process by automating campaign orchestration, enabling real-time progress tracking and reporting. This significantly reduces manual workload while ensuring timely, auditable reviews that support both regulatory compliance and risk mitigation.
Access Reviews & Recertification
Access reviews are a core component of identity governance, involving the systematic verification of users' existing permissions to confirm that access entitlements remain valid and are necessary for their current job functions. These reviews can be conducted on a periodic basis (e.g., quarterly or semi-annually) or initiated in response to contextual risk factors, such as access to sensitive systems, high-risk roles, or specific regulatory requirements. Well-executed review processes help uncover and remediate issues like inactive users, orphaned accounts, and permissions that are excessive or fall outside established policy.
Access recertification expands on access reviews by formally requiring designated reviewers, such as managers, application owners, or data stewards, to attest that users’ assigned permissions are appropriate for their current responsibilities. Recertification becomes particularly important following organizational changes like team transfers, promotions, or new project assignments, helping to prevent privilege creep and uphold least-privilege access models.
Audit & Compliance Logs
Keeping regular audit trails is important for meeting regulatory standards like SOX, GDPR, HIPAA, and ISO 27001. Access certification platforms create logs that record each and every review, approval, rejection, or removal across all campaigns. These logs are important for showing accountability during audits to avoid last-minute stress. Dashboards and reports also give auditors a centralized view of past certifications, any issues, and overall trends.
Preparing For Audits, But Unsure If Access Reviews Will Hold Up?
Use a structured roadmap before the pressure hits.
Key Technologies: IGA Tools for Certification
Identity Governance and Administration (IGA) tools automate access certification using workflows, RBAC, SoD controls, and real-time monitoring to reduce manual effort and strengthen compliance.
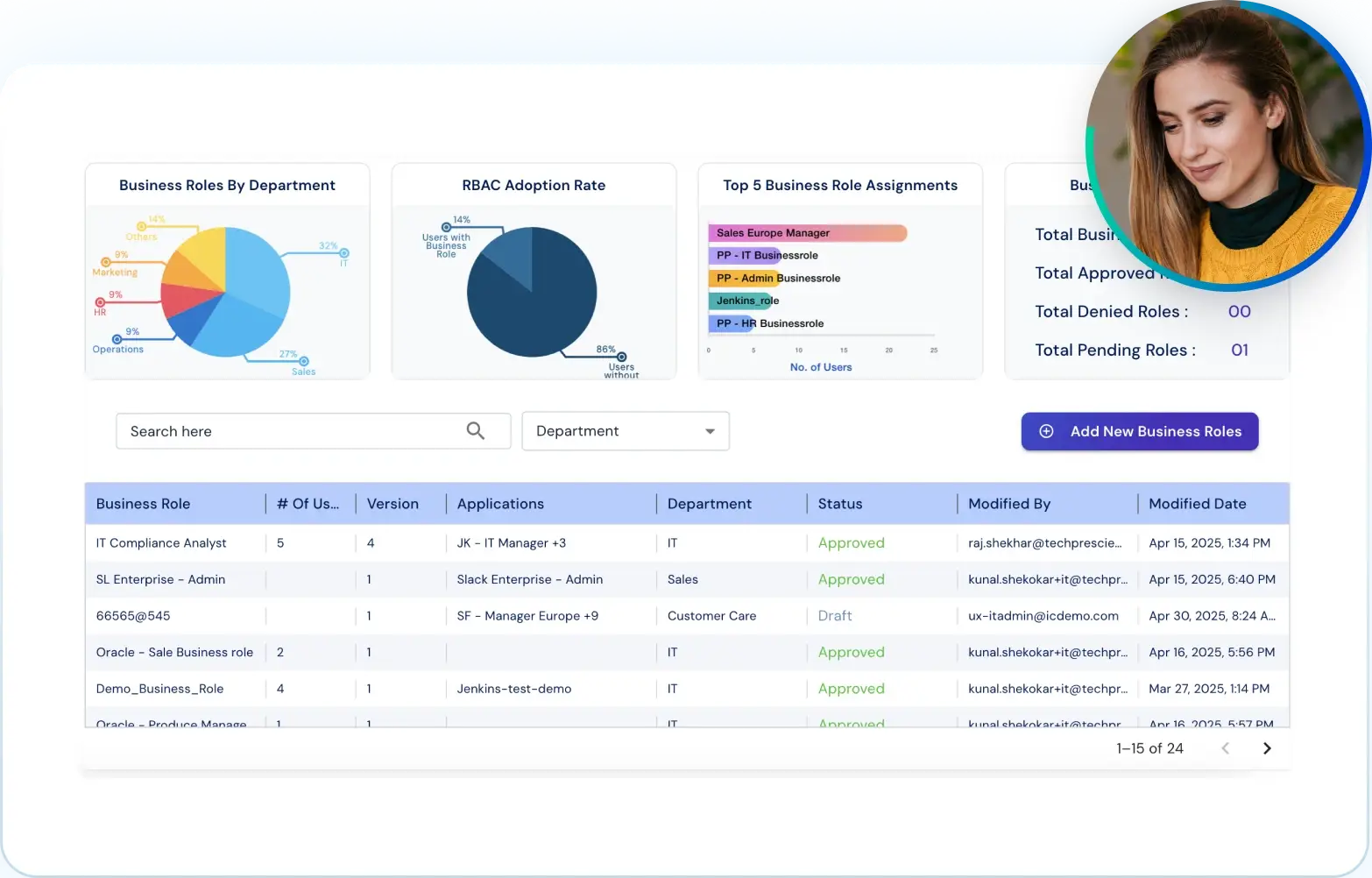
In hybrid and cloud-first environments, access certification cannot be sustained through spreadsheets or email-driven reviews. Modern IGA like Tech Prescient, enable organizations to enforce governance controls systematically while maintaining audit readiness.
Automated Workflows & Scheduled Campaigns
IGA tools streamline the access review process by automating the scheduling of regular campaigns to evaluate user access rights and certifications. This minimizes manual effort while ensuring timely reviews, thereby enhancing both compliance and the organization’s security posture.
RBAC Enforcement
Role-based access control enables access decisions to be aligned with defined job roles rather than individual entitlements. By certifying access at the role level, organizations reduce over-provisioning, simplify reviews, and enforce least privilege more consistently across systems.
SoD Conflict Detection
Segregation of Duties (SoD) controls identify situations where a user holds conflicting access that could enable fraud, misuse, or error. IGA tools continuously evaluate entitlements against SoD policies, allowing reviewers to detect and remediate conflicts before they result in control failures.
Real-Time Alerts & Auto-Remediation
IGA tools provide continuous monitoring of user access and system activity. When potential security threats or policy violations are detected, such as an SoD conflict or unauthorized access, the system can generate alerts and automatically initiate remediation actions, like revoking access or modifying permissions.
Benefits of Effective Access Certification
Effective access certification improves security, reduces identity sprawl, strengthens accountability, and ensures continuous audit readiness.
Effective access certification goes beyond compliance; it strengthens your overall identity security posture and boosts operational efficiency. Conducting regular, structured certification campaigns within an IGA platform enables organizations to:
Strengthen Security Posture
Regular validation of access ensures that unnecessary, outdated, or excessive permissions are identified and removed. This reduces exposure to insider misuse, privilege accumulation, orphaned accounts, and unauthorized access. Early detection through certification enables security teams to address access risk before it results in control failures or incidents.
Reduced Identity Sprawl
Certification processes help detect and remove dormant accounts and outdated roles, enhancing the accuracy of identity repositories and minimizing the organization’s attack surface. This cleanup is particularly critical following role changes, employee exits, or project completion, where residual access often remains. It ensures a leaner, more secure access environment with reduced exposure to threats.
Preparing For Audits, But Unsure If Access Reviews Will Hold Up?
Use a structured roadmap before the pressure hits.
Enhance Cross-Functional Collaboration and Accountability:
Engaging line managers, application owners, compliance officers, and HR in structured certification workflows helps ensure that access reviews are contextually accurate. This distributed attestation enhances accountability, minimizes the risk of oversight, and promotes a culture of shared responsibility in identity governance. It results in more reliable access decisions and stronger overall governance
Streamline Audit Readiness:
Automated certification ensures a defensible audit trail, streamlines the process of gathering evidence for regulatory mandates, and showcases ongoing compliance with standards such as SOX, GDPR, and HIPAA. It simplifies audits and strengthens your organization's regulatory posture
Best Practices for Access Certification in IGA
Following access certification best practices, such as least privilege enforcement, automation, and continuous monitoring, helps organizations scale identity governance securely.
Access certification is most effective when treated as a continuous governance control rather than a periodic administrative task. Consistent application of established practices helps organizations reduce identity risk, maintain compliance, and scale governance as environments grow.
Enforce Least Privilege Through RBAC
Access should be granted and reviewed based on defined roles, not ad hoc requests. Role-Based Access Control (RBAC) aligns entitlements with job responsibilities and provides a stable baseline for certification.
Regular comparison of assigned access against role definitions helps identify over-privileged users and outdated permissions. RBAC also simplifies certification by standardizing access patterns, reducing review complexity, and improving consistency across systems.
Collaborate With Line-of-Business Managers
Access decisions are most accurate when reviewed by stakeholders who understand how access is used. Line-of-business managers and application owners are best positioned to assess whether access remains necessary based on current responsibilities. Involving these reviewers distributes accountability, reduces reliance on centralized IT judgment, and improves the quality of certification outcomes.
Automate With AI-Driven Tools
AI-driven IGA platforms enhance access certification by applying machine learning and analytics to large-scale identity data. These platforms can identify anomalous access patterns, flag excessive or atypical permissions, and surface higher-risk entitlements for focused review.
By establishing behavioral baselines and policy context, AI-driven analysis helps prioritize reviewer attention and reduce decision fatigue. Used appropriately, AI-driven IGA capabilities improve review efficiency and consistency while preserving human accountability for final access decisions.
Monitor Continuously & Audit Often
Access certification should not be isolated to fixed review cycles. Continuous monitoring of access changes and policy violations improves visibility between campaigns and enables faster response to risk.
Ongoing monitoring supports timely adjustments during role changes, offboarding events, and policy exceptions, while ensuring that certification evidence remains current and audit-ready.
Challenge | Solution |
|---|---|
Spreadsheet Fatigue | Use automated IGA tools with workflow templates |
Reviewer confusion or no response | Add training, access context, and dashboards |
Access creep after role change | Use recertification and role-based provisioning |
Blind approvals | Introduce low AI-powered risk scoring |
Lack of audit trail | Ensure logging & reporting via IGA platforms |
Common Challenges and How to Overcome Them
Common access certification challenges include manual fatigue, reviewer inaction, and access creep, all of which can be mitigated using automated IGA workflows and RBAC.
Access certification is the key in modern identity governance, but it often faces challenges that can impact its effectiveness. Several issues, including process fatigue and unclear roles, can weaken your security if not handled properly. Let us look at the most common problems in access certification and how to fix them.
Manual fatigue from spreadsheet-based reviews
Using spreadsheets and emails for access reviews is not only a slow process but also a risky one. Reviewers can get tired of the repetitive work, which will increase the chance of blind approval of access or missing out on something important. To address this, organizations should implement automated access certification processes that enable faster, more accurate reviews, minimizing errors while keeping reviewers engaged and accountable.
Reviewer inaction or confusion
Access reviews are often given to managers or application owners who may not have enough context to make the right decisions, or worse, sometimes do not respond at all. This causes delays and also incomplete reviews. Providing clear training with easy-to-understand dashboards and helpful access details (like user roles, their last login, and how often access is used) can help reviewers certify accurately and also on time.
Access creep from role changes
When users switch between departments or take on new responsibilities, their previous access rights and entitlements are often not fully revoked. This buildup of unnecessary permissions is known as “access creep” or “privilege creep.” Over time, it results in over-provisioning, which increases the risk of unauthorized data exposure, policy violations, and non-compliance with regulatory requirements.
To mitigate access creep, organizations should implement automated, role-based access provisioning (e.g., RBAC), which grants permissions strictly based on users’ current job roles. In addition, conducting regular access recertification or attestation campaigns ensures that access rights are periodically reviewed and updated to reflect personnel and organizational changes. These practices support the principle of least privilege and help proactively reduce compliance and security risks caused by excessive or outdated access.
Reality Check:
If reviewers are approving access in under 10 seconds, they’re not reviewing, they’re clicking. Automation should guide decisions, not rush them.
Access Certification vs. Access Recertification
Access certification validates access at key lifecycle events, while access recertification periodically revalidates existing access to prevent privilege creep and maintain compliance.
Access certification is typically applied at defined points in the identity lifecycle, where access is granted or materially changed. Access recertification is a recurring control designed to revalidate existing access over time. Together, they help organizations enforce least privilege, reduce access risk, and maintain compliance without introducing unnecessary manual overhead.
Quick Comparison: Certification vs. Recertification
Criteria | Access Certification | Access Recertification |
|---|---|---|
Goal | The goal is to grant and validate appropriate access when a user is onboarded or assumes a new role. | The goal is to periodically revalidate existing access to ensure it is still appropriate and necessary. |
Frequency | It is typically performed during onboarding, system rollout, or when new access is requested. | It is conducted on a regular schedule, such as quarterly or biannually, depending on policy. |
Focus | The focus is on ensuring that users receive only the access they need from the start. | The focus is on reviewing whether users still require the access they were previously granted. |
Trigger | It is triggered by events like new hires, implementation of new tools, or organizational changes such as mergers. | It is triggered by scheduled review cycles or compliance-driven requirements. |
Output | The result is access that is approved based on the user’s role and current business needs. | The result is a decision to retain or revoke access based on whether it aligns with the user’s current responsibilities. |
Use Case Examples:
Onboarding a New Employee (Access Certification)
Access certification is commonly used during events such as onboarding, role changes, or access requests. Its purpose is to ensure that newly granted or modified access aligns with job responsibilities and has been explicitly approved by accountable stakeholders.
This initial validation establishes a controlled access baseline and prevents excessive permissions from being introduced at the point of access assignment.
Example: When a new employee joins, access certification confirms that their initial access matches their assigned role, is approved by the appropriate owners, and does not exceed business need.
Quarterly Review for Existing Users (Access Recertification)
Access recertification focuses on access that already exists. It is performed on a recurring schedule, such as quarterly or semi-annually, to confirm that permissions remain appropriate as roles, projects, and risk conditions change.
By requiring reviewers to reattest to existing access, recertification helps detect privilege creep, stale entitlements, and misaligned access that accumulates over time.
Example: During a quarterly review cycle, managers and application owners validate whether users still require their current access or if permissions should be adjusted or revoked due to role changes or inactivity.
What Our IGA Expert Suggests
“Certification is essential to scalable, secure access control in any modern IGA strategy. Without it, you're blind to who can do what inside your organization.”
-Tech Prescient IAM Consultant
At Tech Prescient, we believe that access certification is not just a compliance task but also a key to strong identity governance. In today’s hybrid work culture and cloud-based world, managing access at a large scale needs more than just manual spreadsheets and outdated tools. It requires certification, processes that are not only automated but also smart, trackable, and flexible to fit your business. If done right, access certification gives IT and security teams the visibility and control they need to reduce risks, pass audits, and support Zero Trust. It is not just about technology but also a security-first culture where every access decision is clear, justified, and viewed regularly.
Final Thoughts
Access certification is not just about checking boxes, but it is also about building a security-first culture, which protects what matters the most. When done right, access certification can reduce risks, make compliance easier, and improve collaboration between IT, HR, and different business teams. If you are ready to move past spreadsheets and manual reviews, it is time you explored a smarter approach.
Let Tech Prescient help you automate, improve, and scale your access certification process with confidence.
Book a demo with our identity governance experts today.
Preparing For Audits, But Unsure If Access Reviews Will Hold Up?
Use a structured roadmap before the pressure hits.
FAQs
Access certification is the process of regularly checking who has access to systems and data. It ensures that only the right users keep the right access, helping reduce risks and avoid data breaches. It’s crucial for both security and compliance.
Access certifications are typically done every quarter, six months, or yearly, depending on risk and industry rules. Frequent reviews help catch issues early. The right timing ensures better control and compliance.
IGA platforms such as SailPoint, Saviynt, and Tech Prescient simplify quarterly access certification by automating reviews, providing contextual access data, and generating audit-ready reports.
Yes, laws like SOX, HIPAA, and GDPR require regular access reviews. Certification proves your organization controls access properly. It supports audit readiness and helps avoid compliance penalties.
IGA platforms support access certifications and audits by automating review campaigns, enforcing policies like RBAC and SoD, and maintaining detailed certification logs required for compliance audits.