
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Access control in cybersecurity defines how users, systems, and processes are granted or denied access to data, applications, and infrastructure. The most common access control models include DAC, MAC, RBAC, and ABAC, each designed for different security and compliance needs. Moreover, as digital ecosystems become increasingly dynamic and hybrid, choosing the appropriate access control approach is a strategic requirement. It's a strategic decision with real consequences for security, compliance, and operational efficiency. This blog will review the four core access control types: Discretionary, Mandatory, Role-Based, and Attribute-Based, along with examples, use cases, and how Identity Governance and Administration (IGA) solutions; such as Identity Confluence govern and optimize these models at scale. Access control is typically foundational in identity-first organizations, whether you are securing sensitive customer data, managing access to critical cloud infrastructure, or adhering to increasingly rigorous compliance regulations.
What Is Access Control in Cybersecurity?
Access control in cybersecurity determines which users, systems, or processes can access specific resources, and under which conditions. It ensures that only individuals or processes that are authorized and authenticated to interact with an organization's managed assets, protecting sensitive information while maintaining the confidentiality, integrity, and availability (CIA) of enterprise environments.
Access control consists of identification, authentication, and authorization mechanisms designed to grant or restrict permissions to users to align their privileges with their business role and the organization's policies. In contemporary machine-to-machine interactions, access control and user identity verification can be further augmented to include features such as biometric validation or the utilization of multi-factor authentication (MFA) messages and hardware. Architecture is also enhanced by using a policy-based access framework to define permissions logically and enforce secure, adaptive access across all environments.
Importantly, access control forms the basis for the Zero Trust security model ("never trust, always verify") and regulatory compliance with standards such as HIPAA, SOX, and ISO 27001. And by practicing least privilege, it assists in an organization's efforts to assess insider threat issues and improve operational risk management.
Access control is broadly categorized into two types:
- Physical Access Control: This includes physical access controls such as locks, biometric scanners, and key cards used to restrict access to physical spaces such as offices, data centers, or secured labs.
- Logical Access Control: This includes digital access controls such as file permissions, software restrictions, and operating system access controls to restrict access to data, applications, or network resources based on authenticated credentials and assigned permissions.
Together, these two forms of access controls create comprehensive access restrictions for both physical and cyber environments to enable modern enterprises to operate in a highly agile manner while ensuring adequate access and protection measures, including governance mechanisms.
What Are the 4 Types of Access Control?
The three traditional types of access control are Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role-Based Access Control (RBAC). Attribute-Based Access Control (ABAC) is considered a modern extension.
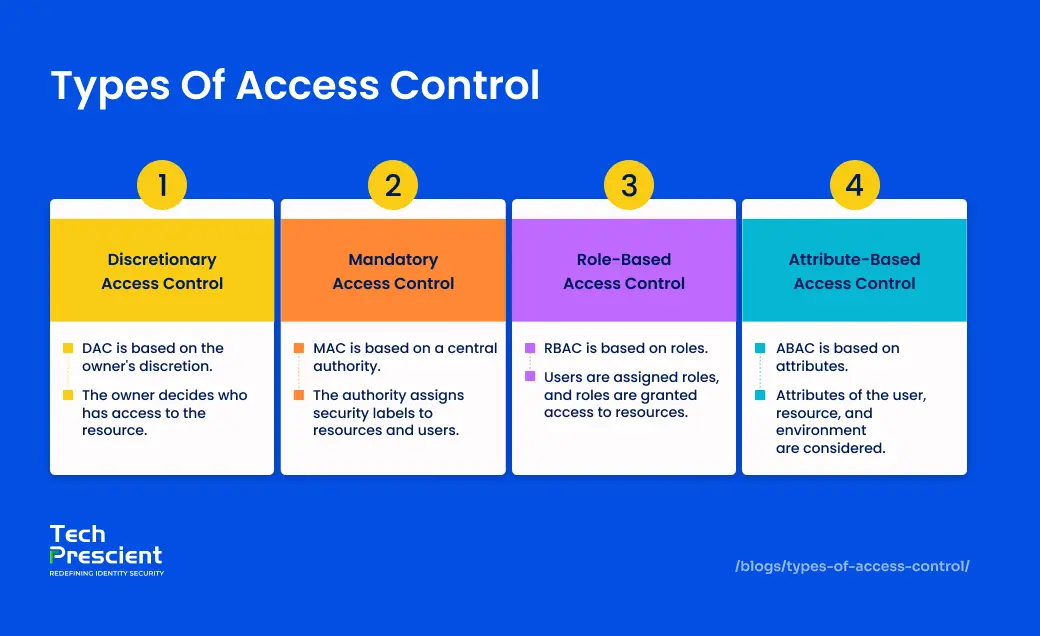
Discretionary Access Control (DAC)
Discretionary Access Control (DAC) allows data owners to decide who can access their files and what actions they can perform. They can freely add or remove users and set permissions for users at their discretion, similar to the user responsibility seen in consumer file-sharing services, including Google Drive and Dropbox. While DAC supports collaboration and high user autonomy, DAC brings a higher risk of potentially unauthorized access to data while allowing individuals within the organization to own the permissions, as formal governance and oversight are often limited in DAC-based environments. DAC works in environments that are highly creative or collaborative, but it should be closely monitored in organizational or enterprise settings.
Security Note:
DAC environments are especially prone to data leakage if sharing permissions are not periodically reviewed or governed centrally.
Mandatory Access Control (MAC)
Mandatory Access Control (MAC) enforces access decisions based on predefined security labels assigned by the system, not the user. Once a user authenticates, they are associated with predefined security attributes - a combination of access attributes that determine, based on the level of classification, what data they can access. Security labels must align with or match in order to grant access, making for highly controlled, traceable data flows.
Because the permissions are not adjustable (non-negotiable) and centrally controlled, MAC limits the possibility for insider threats or accidental exposures of sensitive data. The trade-off of this inflexibility, even for a very high-trust environment, is that it is not easily adaptable to fast-paced business types of environments that require operational flexibility.
Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is one of the most common access models used within enterprises. It provides access based on an individual's user role in the enterprise (e.g., HR manager, IT administrator, Sales associate, etc.). Each role has a defined set of permissions that an enterprise maps to an individual's user account, enabling scalable management of permissions and easier auditing. From an operational standpoint, RBAC enhances efficiency and supports simplified onboarding/offboarding workflows. However, poorly governed RBAC implementations can result in role explosion with resultant over-permissioning of roles.
Pro Tip:
RBAC simplifies access at scale, but without lifecycle governance, roles often accumulate permissions over time, leading to role sprawl.
Attribute-Based Access Control (ABAC)
Attribute-Based Access Control (ABAC) is a dynamic, context-aware access control model that grants users permission based on attributes such as department, job title, device type, geographic location, time of day, etc. Attributes overall represent a user's digital profile, and access is granted when user attributes meet the conditions of a policy. For instance, a doctor may not be allowed to access electronic health records except when logged in from a device issued by the hospital during working hours, which ABAC could administer in seconds. Unlike RBAC, which relies on static role assignments, ABAC evaluates access dynamically. ABAC allows more nuanced, risk-intelligent, fine-grained decisions that are always contextualized.
ABAC systems are particularly valuable in cloud-native and hybrid IT environments, where users, devices, and data are constantly shifting across environments. ABAC allows for policies that apply automatically to those shifts, allowing for better security while not disrupting user productivity. ABAC policies are a form of policy enforcement; organizations create separate policies to evaluate with logical conditions based on attributes. Policy evaluations occur dynamically and in near real time. These attributes can also come from external systems like HR databases, marketing CRMs (e.g., Salesforce), or even identity provisioners. The link between the external context of the user and the internal hierarchy adds additional semantic context as to what we want and how risk is articulated.
While ABAC has great potential, strong policy governance and oversight are needed for it to be utilized fully. When rules are defined correctly, but with conflicting attributes, organizations may grant over-permissions or, alternatively, deny access. Documentation, testing, and validating ABAC are crucial.
Access Control Models Comparison Table
| Model | Definition | Key Characteristics | Example Use Case |
|---|---|---|---|
| DAC | Access is granted by the data owner at their discretion | User-centric, flexible, but less secure, prone to inconsistent enforcement | A member of the group shares a folder in Google Drive with a few selected collaborators. |
| MAC | Access is enforced based on system-classified security labels | System-controlled, non-negotiable; ideal for highly classified data | Access to "Top Secret" forms of documents with military-grade levels of clearance, by user clearance. |
| RBAC | Access is assigned based on user roles within an organization | Scalable, easy to manage and audit; widely adopted in enterprise environments | HR managers access the payroll systems using pre-assigned HR roles. |
| ABAC | Access is determined by evaluating attributes (e.g., user, device, location, time) | Context-aware, flexible, supports fine-grained policy enforcement | Doctors access electronic health records from only hospital IPs while they are on duty/working. |
Understanding the differences between DAC, MAC, RBAC, and ABAC is one thing; choosing the right model for your environment is another.
The Right Access Model Changes Everything
Compare models and find the right fit for your organization's risk, governance, and compliance needs.
Other Access Control Models to Know
Beyond DAC, MAC, RBAC, and ABAC, organizations also use policy-based and risk-adaptive access control models. Understanding these helps organizations adapt to evolving security needs:
- Policy-Based Access Control (PBAC): PBAC extends the principles of RBAC and ABAC by incorporating business logic and compliance policies directly into access decisions. For example, access might only be granted if a specific workflow step is completed or during a defined audit period. It's particularly useful for highly regulated industries that require dynamic access governance.
- Risk-Adaptive Access Control (RAdAC): RAdAC takes access control a step further by integrating real-time risk signals such as threat intelligence or user behavior analytics into the decision-making process. If a user logs in from an unusual location or attempts to access sensitive data outside normal hours, RAdAC can restrict or deny access dynamically.
- Identity-Based Access Control (IBAC): This model grants access based solely on the authenticated identity of a user. It's straightforward and commonly seen in legacy systems but lacks the contextual awareness of modern models. IBAC often serves as a foundational layer that can be enhanced by adding roles or attributes.
- Access Control Lists (ACLs): At the object level, ACLs describe permissions on Unix-like operating systems, which in this case are folders or files. Each object has a list of users or systems who can read, write, or execute that object. In smaller, well-scoped environments, ACLs are effective, as they allow precise management of resources. However, in larger environments, oversight can be tedious and cumbersome if ACLs are not centrally managed.
- Principle of Least Privilege (PoLP): Rather than a model, PoLP is a philosophy that supports all access control systems, which says the user should only have access to the resources they absolutely need to perform their job. By implementing PoLP to limit access, you can limit your exposure and reduce the operational impact of a breach, and to an organization, it is a good practice for compliance audits.
Ready to move beyond basic access models?
See how enterprises combine RBAC, ABAC, and PBAC under unified governance frameworks.
Real-World Use Cases by Access Control Type
It's important to recognize how each access control model operates in a real-world situation. This is crucial in considering the favorable/detrimental aspects of an access control model to determine if it is the right access control strategy for a given organization's particular needs. Here is an outline of industries/scenarios mapped against these models:
| Type | Use Case | Example |
|---|---|---|
| DAC | File sharing | Google Drive folder permissions |
| MAC | Military data | Access labeled "Classified." |
| RBAC | HR systems | Payroll access for the HR team |
| ABAC | Healthcare | Access only from verified hospital IP during work hours |
These practical examples demonstrate that good model selection positively impacts security, operational efficiency, and compliance posture across diverse industries.
Conclusion
Selecting the appropriate access control model is not a one-size-fits-all process. While DAC, MAC, RBAC, and ABAC are all able to meet different security requirements, the challenge lies in getting them operational in multiple, complicated, hybrid environments. This is where Identity Governance solutions such as Identity Confluence provide value, allowing enterprises to define, manage, enforce, and monitor access changes dynamically, while creating consistent policy enforceability, maintaining strong audits, and maintaining continuous audit readiness.
Don't just understand access control, implement it.
Learn how leading enterprises operationalize DAC, MAC, RBAC and ABAC with IGA solutions like Identity Confluence.
FAQs
The traditional core three types are Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role-Based Access Control (RBAC). Attribute-Based Access Control (ABAC) has emerged as a fourth model and is widely adopted in modern, dynamic environments.
Role-Based Access Control (RBAC) is associated with a user's organizational role, which makes RBAC relatively static. Attribute-Based Access Control (ABAC) implements access control based on real-time attributes, such as time, location, or the device being used, thus allowing for dynamic enforcement, which includes finer granularity.
Due to its centrally enforced, classification-driven rules and access granted by classification, MAC has the highest level of security and is useful for environments with highly sensitive data.
IGA solutions, such as Identity Confluence, extend all access models - including RBAC, ABAC, ACL, and MAC - by automating provisioning, performing access reviews, enforcing governance policies, and producing compliance-ready audit history and audit trails reports from a centralized dashboard while providing a secure, scalable, and continuously governed access process across both on-premise and cloud resources.
Yes, most enterprises today operate in hybrid environments where multiple access control or permission models exist, including RBAC for intended structured access based on pre-determined internal roles, ABAC for contextual and condition-based decisions in cloud systems, ACLs for older and often legacy applications or databases, and MAC for datasets that may need a regulatory role or restriction (i.e., lessons learned with sensitive data such as financial and healthcare).
In zero trust as a concept, access control is a fundamental requirement. Access control supports Zero Trust through contextual ABAC checks, predefined RBAC least-privilege access, and continuous monitoring with policy violation detection and real-time reviews.
Access certification helps to ensure that access permissions stay current over time - especially after role changes, project completions, or user exits.
Some common signs that access may be a problem include inactive access, revocation delays, role sprawl, unknown approvals, and missing logs leading to failed audits.
Brinda Bhatt
Digital Marketing Strategist
Specializes in translating complex identity governance and access management concepts for both business and technical audiences. Her work is grounded in a logical, data-driven approach, with a focus on clear, outcome-driven technical storytelling.
Most Popular Blogs

Identity Security· 33 min read
What Is an Orphaned Account? Definition, Risks & Fixes
Orphaned accounts are hidden cybersecurity risks. Learn what they are, how they arise, and how to eliminate them securely with IAM best practices.
Brinda Bhatt· May 26, 2026

