On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
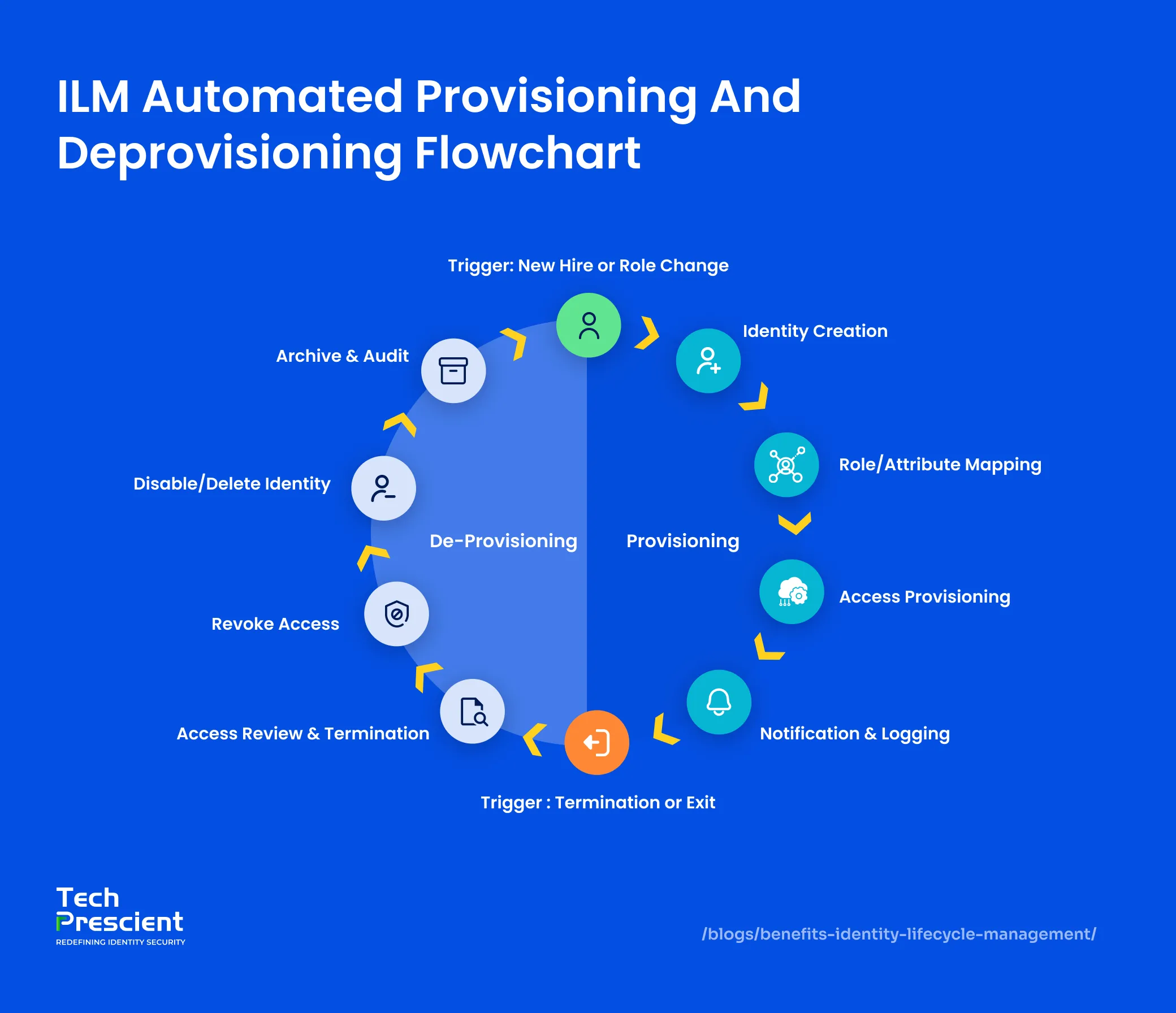
As organizations scale across cloud platforms, SaaS applications, and hybrid work environments, managing user access efficiently becomes a business-critical challenge. Identity Lifecycle Management (ILM) delivers measurable benefits by automating how identities are provisioned, updated, and removed, reducing risk, operational overhead, and compliance gaps.
Enterprises adopt Identity Lifecycle Management to address practical challenges such as delayed onboarding, excessive access, audit failures, insider risk, and rising IT costs. ILM addresses these challenges by enforcing least-privilege access, eliminating manual identity processes, and maintaining continuous visibility across the identity lifecycle.
Organizations undergoing rapid hiring, mergers, regulatory pressure, or cloud expansion rely on ILM to stay secure and compliant, without slowing productivity. If you’re looking to understand the fundamentals of ILM, explore our detailed guide on what Identity Lifecycle Management is and how it works. Otherwise, the sections below outline the most impactful benefits ILM delivers for modern enterprises.
Key Takeaways:
- Automates identity provisioning and deprovisioning to eliminate manual errors and delays
- Reduces security risk by enforcing least-privilege access and removing excessive permissions
- Lowers IT operational costs by minimizing tickets, rework, and manual identity tasks
- Simplifies regulatory compliance with automated access reviews and audit-ready reporting
- Improves employee productivity with faster onboarding and self-service access
- Provides centralized visibility into user access across cloud apps, systems, and endpoints
Top 10 Benefits of Identity Lifecycle Management (ILM)
A well-implemented Identity Lifecycle Management (ILM) strategy simplifies the lives of IT teams and end users by streamlining user access, mitigating risks, and enhancing compliance.
1. Enhanced Security through Automated Access Controls
Identity Lifecycle Management reduces the attack surface by ensuring access is granted based on role, context, and policy, and removed automatically when no longer needed. By integrating with HR systems, directories, and identity sources, ILM automates provisioning and deprovisioning without manual delays or errors.
When employees join, change roles, or leave, access is updated in real time. This prevents privilege creep, reduces insider risk, and ensures access remains aligned with current responsibilities.
Pro Tip
Automating provisioning without lifecycle enforcement still creates risk. ILM delivers security only when access is continuously adjusted as roles, attributes, and employment status change.
2. Improved Operational Efficiency
Manual identity processes are slow, costly, and risky. But with Identity Lifecycle Management, automation can turn weeks of provisioning/deprovisioning work into minutes. Automated ILM significantly reduces onboarding and access change timelines, allowing IT teams to move from manual ticket handling to policy-driven automation.
With Identity Lifecycle Management, as soon as a new hire joins your organization, access is automatically provisioned via Role-Based Access Control (RBAC). By automating role-based access, ILM removes delays during onboarding, role changes, and access updates, improving efficiency across IT and business teams.
See Identity Lifecycle Automation in Action
Explore real-world ILM scenarios that eliminate delays, risk, and manual effort.
3. Simplified Regulatory Compliance
Simplified Regulatory Compliance is a key benefit of Identity Lifecycle Management, especially for organizations operating under regulations such as GDPR, SOX, HIPAA, and ISO standards. ILM enforces policy-based access, maintains continuous audit trails, and automates access reviews, ensuring organizations are always audit-ready.
ILM ensures that only authorized users can access sensitive data while supporting segregation of duties and access governance requirements. Automated reporting and access reviews reduce audit preparation time and help organizations respond to compliance requests with confidence.
4. Reduced IT Costs
Identity Lifecycle Management reduces IT costs by automating identity tasks, lowering ticket volumes, and eliminating redundant or outdated access. This allows IT teams to focus on higher-value initiatives instead of manual access management. Simultaneously, ILM constantly eliminates orphaned accounts and ensures users only have the right access to the right resources, minimizing the risk of costly security breaches.
IBM reported that the average cost of a data breach reached $4.45 million, and the most common factor in the initial attack was compromised credentials. ILM automates access clean-up and enforces periodic deprovisioning that significantly reduces this risk.
By enforcing least-privilege access and regular entitlement reviews, ILM also reduces the likelihood of costly security incidents tied to excessive or unmanaged access.
5. Insider Threat Mitigation
Insider threats, whether accidental or intentional, often stem from excessive or outdated access. Identity Lifecycle Management addresses this risk by enforcing least-privilege access and continuously monitoring permissions throughout the user lifecycle.
What does ILM do to curb insider threats?
- Supports Segregation of Duties (SoD)
- Automates access reviews to catch risky entitlements
- Tracks user roles or employment status changes
- Revokes access immediately when the user status changes
6. Improves User Experience with Faster, Self-Service Access
Improved user experience is a direct outcome of effective Identity Lifecycle Management. By automating onboarding, role-based access, and approvals, ILM ensures employees receive the access they need from day one, without delays or IT bottlenecks. ILM also enables self-service access requests and automated approvals, ensuring users receive timely access through clearly defined policies.
What are the user experience benefits of ILM?
- Self-service access lessens IT dependency
- Faster day-one access when onboarding
- Fewer support tickets for access problems
- Smooth transitions during role changes
7. Centralized Visibility and Control Across the Identity Lifecycle
Centralized visibility across the identity lifecycle allows organizations to clearly understand who has access to what, and why, at any given time. Without this centralized visibility, IT teams have to depend on guesswork and fragmented data to understand who has access to what. With ILM’s centralized dashboards and identity repositories, organizations can spot anomalies, access patterns, and implement policies all in one place.
Why centralized visibility matters:
- Easy implementation of SoD (Segregation of Duties) and least privilege
- Simplified reporting for compliance and audits
- Real-time insight into user access
- Flagging of dormant or over-provisioned accounts
8. Reduced Authentication Friction and Access Support Overhead
Identity Lifecycle Management reduces authentication friction and IT support overhead by streamlining access experiences through self-service password resets, SSO, and consistent access policies across the user lifecycle.
With this, users gain access quickly without needing IT support, while IT teams don’t have to deal with as many password-related tickets. Identity lifecycle management fortifies your complete security posture and increases productivity by enforcing unified password policies across cloud and on-prem environments and reducing irrelevant logins. This reduces access-related disruptions for users while allowing IT teams to focus on higher-priority security and operational work.
Want to understand how ILM works in detail?
Read our complete guide to Identity Lifecycle Management.
9. Adaptability to Change in Dynamic Business Landscapes
Organizational change is constant across growing enterprises. New hires, role changes, mergers, or organizational restructuring. Without automated identity controls, these changes can introduce security gaps, access inconsistencies, and operational delays. This adaptability is especially critical for organizations undergoing mergers, rapid hiring, or cloud expansion
ILM allows your identity infrastructure to grow and scale with your business. For example, when a finance manager is promoted to a senior manager role, ILM automatically updates their permissions, removing any outdated access and provisioning new ones based on defined policies.
With ILM, you can automate user access based on role changes, take care of bulk provisioning (for instance, during mergers and acquisitions), and even ensure compliance with evolving regulations.
10. Audit Readiness Made Easy
Regulatory audits are time-consuming and require accurate, well-maintained access records. But when identity records are ill-maintained or outdated without clear access trails, it can cause harm to your organization’s reputation. Identity Lifecycle Management makes your organization audit-ready by maintaining automated, timestamped details of user access, approvals, and changes across the identity lifecycle.
This guarantees that you always have a real-time view of who has access to what, when, and why. ILM enables your organization to build trusted relationships with customers, investors, and partners while showing strong governance. This level of audit readiness strengthens trust with regulators, customers, and business stakeholders alike.
Best Practice
Audit readiness isn’t about preparing once a year. ILM ensures access to evidence is continuously captured, validated, and reviewable, so audits become routine, not disruptive.
Why Identity Lifecycle Management Is a Business Imperative
Identity Lifecycle Management is no longer just an IT efficiency upgrade, it’s a strategic requirement for securing access, controlling risk, and scaling with confidence. As organizations adopt cloud platforms, expand workforces, and face increasing regulatory pressure, manual identity processes simply don’t scale.
By automating access across the entire identity lifecycle, ILM reduces security gaps, lowers operational costs, improves compliance, and delivers a smoother experience for both users and IT teams. The result is stronger governance without slowing business velocity.
Organizations that invest in Identity Lifecycle Management build a stronger foundation for long-term security, compliance, and operational scale.
From ILM Benefits to Real Execution
See how automated identity lifecycles work across onboarding, changes, and exits.
FAQs
Identity Lifecycle Management reduces security risk by enforcing least-privilege access, automating access removal during role changes or exits, and eliminating orphaned or excessive permissions. This minimizes attack surfaces and lowers the risk of insider threats and credential misuse.
ILM simplifies compliance by automating access reviews, maintaining audit-ready logs, and enforcing policy-based controls required for regulations such as GDPR, HIPAA, SOX, and ISO standards. This reduces manual effort and audit failures
By automating provisioning, deprovisioning, and access updates, ILM reduces IT tickets, manual rework, and security incidents, leading to lower operational costs and improved efficiency across IT teams.
ILM delivers the greatest value for organizations with growing workforces, cloud and SaaS adoption, strict compliance requirements, or frequent role changes, where manual identity management no longer scales securely.
IAM focuses on authentication and access, while IGA governs access through policies and reviews. Identity Lifecycle Management automates how identities are created, updated, and removed across these systems. Learn more about how ILM works in our complete Identity Lifecycle Management guide.
Rashmi Ogennavar
Content Strategist
Rashmi is a Content Strategist at Tech Prescient, translating complex Tech and SaaS concepts into compelling narratives for business and technical audiences. With a strategic, data-informed approach, the work bridges content and product storytelling, crafting messaging that resonates and drives decisions across the buyer journey.
Most Popular Blogs

Identity Security· 14 min read
Identity Management Best Practices to Strengthen Cybersecurity in 2026
Knowing Identity and Access Management (IAM) best practices is essential for improving your organization's security strategy. Learn how MFA, RBAC, and Zero Trust help.
Yatin Laygude· May 4, 2026