IAM vs IGA vs PAM:What’s the Difference in Identity Security?
Learn how IAM, IGA, and PAM differ, why they matter,and how to use them together to secure access, ensure compliance, and enforce Zero Trust for privileged accounts.
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Last Updated date: April 7, 2026
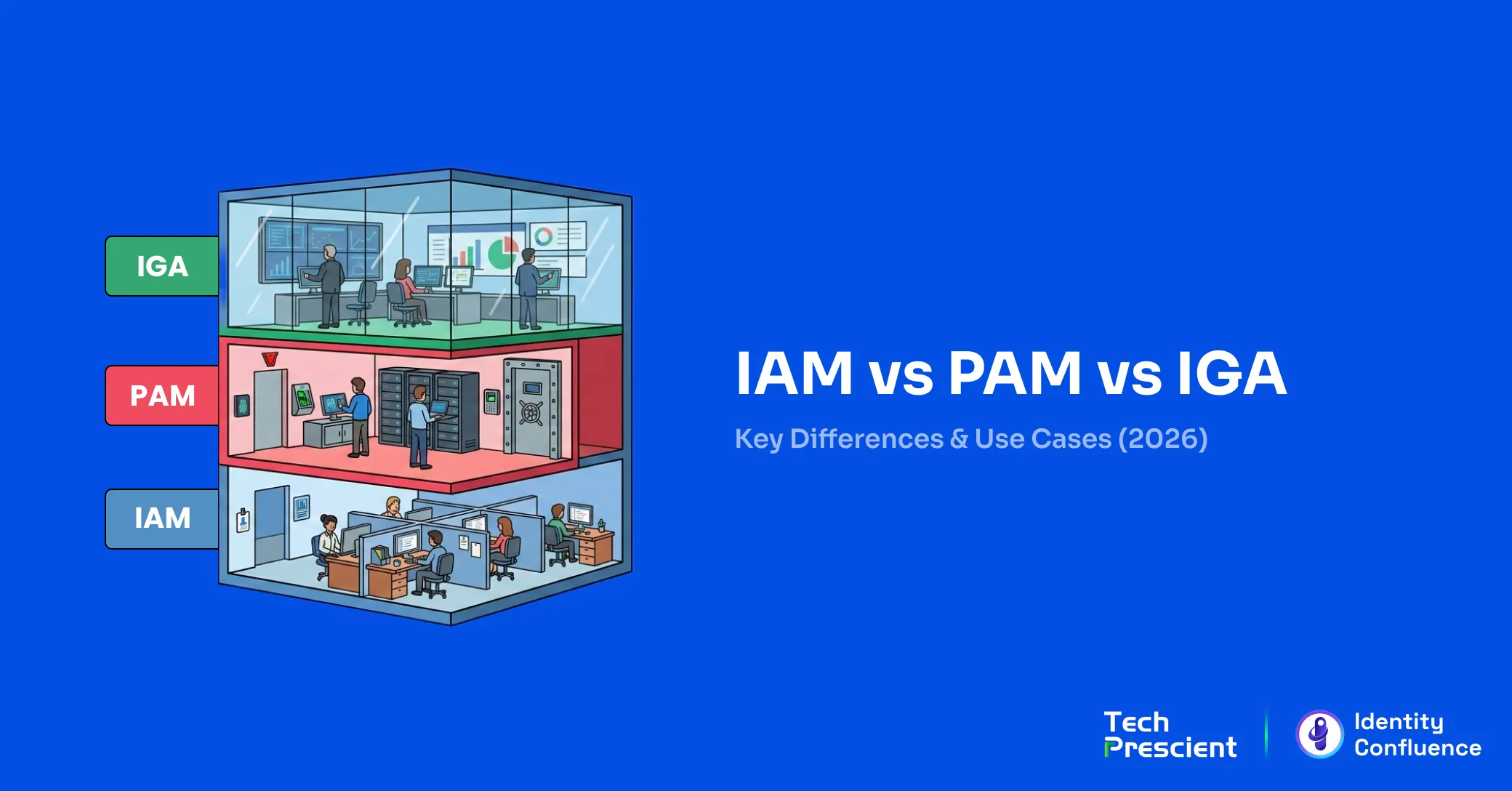
In today’s digital-first environment, identity has become the primary security perimeter. As organizations adopt cloud services and Zero Trust models, controlling who can access systems, applications, and data is critical. IAM, IGA, and PAM form the foundation of a modern identity security strategy. IAM controls access, IGA governs that access for compliance, and PAM secures high-risk privileged accounts.
Identity and Access Management (IAM) is the operational layer of identity security. It determines who can access which resources and under what conditions. IAM manages authentication and authorization through capabilities such as user provisioning, Single Sign-On (SSO), Multi-Factor Authentication (MFA), and role-based access control.
Whereas, PAM (Privileged Access Management) adds an extra layer by securing high-risk, privileged accounts such as admin or root accounts through strict access controls, session monitoring, privilege elevation, password rotation and credential vaulting.
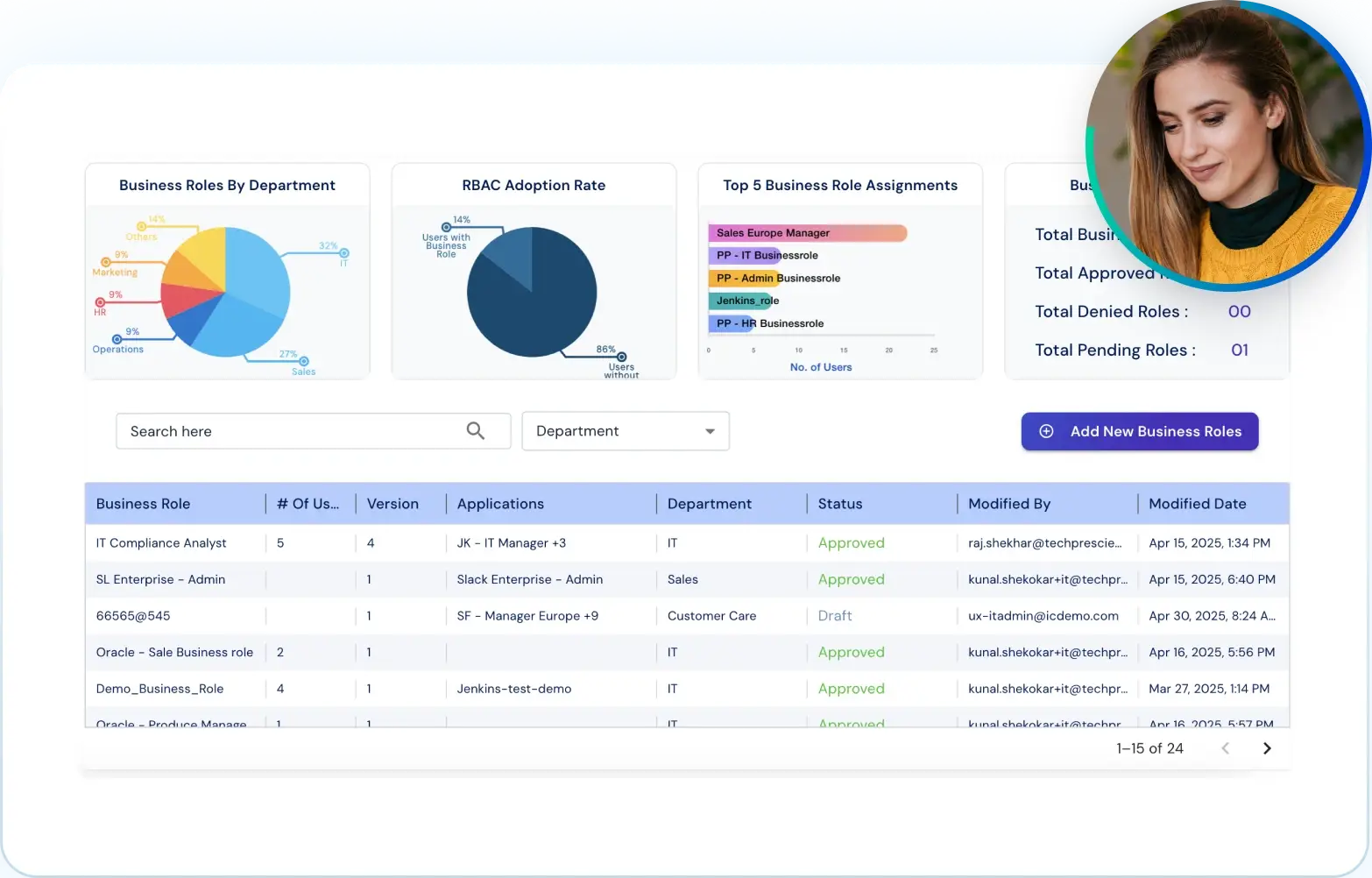
Talking about, IGA (Identity Governance and Administration), it provides oversight by governing access rights across the organization, ensuring they comply with internal policies and external regulations. This can be done through processes like access reviews, certifications, and role lifecycle management.
Although all of the above are more so viewed in isolation, but the real power comes when they work together, while balancing access control, privileged account protection, and identity governance. In this blog we will be focussing on understanding the difference between IAM and IGA and PAM, which is the key to building a resilient, Zero Trust-ready cybersecurity framework.
Key Takeaways:
- IAM controls user access to systems and applications based on roles and policies.
- IGA ensures that access is compliant, auditable, and governed across the identity lifecycle.
- PAM protects privileged accounts with advanced controls like JIT access, vaulting, and session monitoring.
- Using IAM, IGA, or PAM in silos can lead to security blind spots and compliance risks.
- A unified identity strategy combining all three strengthens your Zero Trust posture.
- Automating provisioning, access reviews, and privileged session monitoring is essential.
- Integration between IAM, IGA, and PAM improves visibility, reduces risk, and supports cloud identity security.
What Is IAM (Identity and Access Management)?
IAM is the system that controls who can access applications and data, while IGA governs whether that access is appropriate and compliant, and PAM secures high-risk privileged accounts.
Identity and Access Management (IAM) is considered as the backbone of modern identity security. IAM ensures that the right individuals, who could be an employee, contractor, or partner can gain access to the right systems and its data at the right time, and for the right reasons.
When we talk about IAM, it primarily handles core functionalities such as user provisioning, authentication, Single Sign-On (SSO), Multi-Factor Authentication (MFA), and policy-based authorization. These not just streamline user access but also reduces risk by enforcing enterprise identity protection and minimize any unauthorized entry points.
Key Functions of IAM:
- User provisioning and deprovisioning
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Role-based access control (RBAC) and policy enforcement
IAM in Action:
When a new employee joins the HR department, IAM automatically provisions their account, enables SSO to approved HR applications, enforces MFA, and restricts access based on role requirements.
IAM serves as a critical layer in your broader identity management strategy, especially when implementing Zero Trust access and maintaining IAM compliance.
Common IAM Mistake:
Treating IAM as “set and forget.” Without governance, IAM often becomes a fast way to provision access but a slow way to remove it.
What Is IGA (Identity Governance and Administration)?
Identity Governance and Administration (IGA) builds on IAM by adding governance, visibility, and compliance controls. While IAM grants access, IGA ensures that access remains appropriate, reviewed, and policy-compliant over time.
IGA helps manage identity-related risks, enforce segregation of duties (SoD), and streamline compliance efforts through scheduled access reviews, certification workflows, and extremely helpful during detailed audit trails.
Key Functions of IGA:
- Access certification and reviews
- Role mining and entitlement management
- Segregation of duties enforcement (SoD)
- Compliance reporting and audit readiness
- Identity lifecycle governance
Why Security Teams Care:
Most breaches don’t happen because access wasn’t controlled. They happen because access was never reviewed.
IGA in Practice:
In organizations handling sensitive or regulated data, IGA enables scheduled access reviews where managers certify user access based on role necessity and policy alignment.
IGA is important for maintaining any type of accountability, it reduces all forms of insider threats, and supports a strong identity management strategy within any cybersecurity framework.
What Is PAM (Privileged Access Management)?
Privileged Access Management (PAM) Privileged Access Management (PAM) focuses on securing accounts with elevated permissions, such as administrator, root, and service accounts. These identities have broad access and represent high-value attack targets.
Unlike IAM, which manages general user access, PAM zeroes in on privileged accounts, limiting their use through strict access policies, time-bound permissions, and real-time oversight. This helps prevent misuse, whether from insider threats or compromised credentials.
Key Functions of PAM:
- Just-in-Time (JIT) access provisioning
- Privileged session monitoring and recording
- Password vaulting and automated credential rotation
- Role-based access control for high-privilege users
- Threat detection and rapid response
Reality Check:
If a compromised admin account can access production systems without session recording, your blast radius is unlimited.
PAM in Practice:
When an administrator requires access to a production system, PAM grants time-bound access for the approved task, records the session, and automatically revokes permissions when the task is complete. All the activities performed by individuals are recorded for auditing, and automatically revoked afterwards. Credentials are stored in a secure vault and rotated regularly to reduce risk.
PAM strengthens cloud identity security, enhances insider threat prevention, and plays an important role in Zero Trust and digital identity control strategies.
IAM vs IGA vs PAM – A Feature Comparison
IAM manages access, IGA governs it, and PAM secures privileged credentials. This table highlights how they differ.
| Feature | IAM (Identity and Access Management) | IGA (Identity Governance and Administration) | PAM (Privileged Access Management) |
|---|---|---|---|
| Focus | Primarily focuses on managing and controlling user access to systems and applications. | Emphasizes governance activities and compliance enforcement related to user access. | Concentrates on managing and securing privileged accounts and their elevated permissions. |
| Target Users | Designed to manage access for all users across the organization. | Applies to all users but with a governance and certification emphasis. | Specifically targets administrators and users with high-risk or privileged access rights. |
| Automation | Automates access provisioning processes and enforces multi-factor authentication (MFA) to secure access. | Automates periodic access reviews and enforces segregation of duties (SoD) policies. | Provides just-in-time (JIT) access approvals and controls privileged session activities. |
| Primary Goal | The main goal is to efficiently grant appropriate access to users based on their roles. | The primary objective is to govern, certify, and maintain compliance over access entitlements. | Aims to secure and tightly control elevated access to prevent misuse of privileged accounts. |
Still unsure whether you need IAM, IGA, PAM, or all three?
Use our decision framework to map the right identity controls to your risk, scale, and compliance needs.
How IAM, IGA, and PAM Work Together
A strong identity management strategy doesn’t just rely on any one of these solutions. It brings together IAM to manage access, IGA to govern that access, and PAM to secure accounts with elevated privileges. Together, they form a layered approach to enterprise identity protection, reducing risk, ensuring compliance, and increasing visibility across the organization.
While IAM handles who gets access and when, IGA ensures that access is appropriate, regularly reviewed, and policy-compliant. PAM steps in to tightly control and monitor access to sensitive systems, aligning the organization with the principle of least privilege a core pillar of Zero Trust access.
IAM + IGA + PAM in Action
Use Case: A financial services firm operating in a cloud-first environment with multiple privileged accounts and strict regulatory requirements.
- IAM provisions new users, enforces Multi-Factor Authentication (MFA), and enables Single Sign-On (SSO) to key applications.
- IGA governs user roles with periodic access reviews, detects toxic combinations through segregation of duties (SoD) policies, and maintains audit trails for compliance.
- PAM secures privileged access to critical systems like production databases and cloud infrastructure. It provides Just-in-Time access, password vaulting, and real-time session monitoring.
Zero Trust Alignment:
The organization applies the principle of least privilege, allowing users only the access they need, when they need it. With governance from IGA and access control from IAM and PAM, the enterprise builds a resilient Zero Trust architecture rooted in visibility, policy enforcement, and identity-driven defense.
Common Pitfalls When Using IAM, IGA, or PAM in Silos
While IAM, IGA, and PAM are powerful on their own, using them in isolation can lead to serious identity security gaps.
- IAM without periodic access reviews can result in overprovisioned users and unnecessary access lingering across systems.
- No PAM for DevOps or admin accounts leaves critical infrastructure exposed to insider threats and credential misuse.
- Lack of visibility across the identity lifecycle prevents security teams from tracking who has access, why they have it, and whether it should be revoked.
When IAM, IGA, and PAM are disconnected, you lose the context and control needed for a mature identity management strategy and effective cybersecurity framework.
Still unsure whether you need IAM, IGA, PAM, or all three?
Use our decision framework to map the right identity controls to your risk, scale, and compliance needs.
Best Practices for Implementing IAM, IGA, and PAM Together
Integrating IAM, IGA, and PAM leads to stronger governance, reduced risk, and a more secure cloud environment. Here’s how to do it right:
- Define user roles and identity lifecycle flows to avoid unnecessary access and enforce Zero Trust access.
- Automate provisioning, access certification, and Just-in-Time (JIT) privileged access to eliminate manual errors and improve scalability.
- Continuously monitor privileged sessions to detect and respond to suspicious activity in real time.
- Ensure tight integration between your IAM, IGA, and PAM platforms so identity data flows seamlessly and policies remain consistent across systems.
Following these best practices helps organizations build a unified and proactive approach to digital identity control, IAM compliance, and enterprise identity protection.
Implementation Tip:
Start integration with IGA at the center. Governance should inform IAM provisioning and PAM approvals, not the other way around.
Final Thoughts: Build a Complete Identity Security Framework
Securing digital identities requires a unified approach where IAM, IGA, and PAM operate together. IAM controls access, IGA governs it, and PAM secures privileged identities. When implemented as a single strategy, these layers strengthen Zero Trust enforcement and support audit readiness.
At Tech Prescient, we help forward-thinking organizations bring these layers together through modern, scalable identity solutions. Whether you're building from scratch or optimizing your current stack, our platform supports a seamless, policy-driven identity security framework tailored to your needs.
Book a Demo Ready to see how IAM, IGA, and PAM can work together in your environment? Book a live demo with our experts and take the first step toward complete identity security.
Still unsure whether you need IAM, IGA, PAM, or all three?
Use our decision framework to map the right identity controls to your risk, scale, and compliance needs.
FAQs
IAM (Identity and Access Management) focuses on authenticating users and managing their access to systems. IGA (Identity Governance and Administration) adds oversight, ensuring access is appropriate, compliant, and aligned with policies. Simply put, IAM manages the how of access, while IGA governs the why.
Privileged Access Management (PAM) is related to IAM but focuses specifically on securing, monitoring, and controlling privileged accounts. While IAM covers general user access, PAM provides extra controls for high-risk accounts like admins and system operators.
Yes. Together, they provide comprehensive identity security: IAM handles access, IGA ensures governance and compliance, and PAM secures privileged accounts. Using all three reduces risk, ensures regulatory compliance, and enforces Zero Trust principles.
Zero Trust requires verifying every identity and controlling access continuously. IAM authenticates users, IGA audits and enforces policy compliance, and PAM restricts privileged access. Combined, they prevent unauthorized access and minimize lateral movement within networks.
Highly regulated and high-risk industries benefit most, including finance, healthcare, government, and large enterprises. These sectors handle sensitive data, face strict compliance requirements, and require robust controls over privileged accounts
A segregation of duties matrix is a visual tool that maps roles against critical tasks to identify conflicts. It helps organizations detect risky role combinations and is commonly used during audits to demonstrate compliance with internal controls and regulations like SOX.
IAM, IGA, and PAM provide audit trails, access certifications, and policy enforcement, making it easier to demonstrate compliance with regulations like HIPAA, GDPR, SOX, and PCI-DSS. They also reduce the risk of non-compliance penalties and security breaches.